To make sure that in addition to the decorative function of the router copes with its main task, pay attention only to products from well-known brands. Top manufacturers of stylish routers: Samsung, D-Link, Apple, ASUS, Google, AmpliFi.
- TAP or SPAN? Recommendations for traffic mirroring for professionals
- SPAN or TAP? Here's the question!
- The main considerations regarding the requirements for full visibility of the real network
- Moment one: the "spy" mirror
- Moment two: hidden cameras in rooms
- Causes of interference with the WI-FI signal
- 8 Ways to Strengthen the WI-FI Signal from the Router
TAP or SPAN? Recommendations for traffic mirroring for professionals
Full network visibility is the foundation of monitoring, management and information security. If you can't see problems such as network attacks, unauthorized use, application inefficiencies, etc., how are you going to identify and effectively address them?
Today's networks are getting bigger and more complex, transmitting unprecedented amounts of data at increasing speeds. There are many times more frames in today's networks than there were 20 years ago, and we moved from 10 Mbps to full-duplex 1, 10, 40, 100 Gbps long ago. This is the era of total data security, deep packet inspection (DPI), legal and policy compliance, network auditing and lawful interception (SORM), which requires tracking all data, not just "sampling" it. All of this makes ubiquitous access to packet-level traffic problematic, at a time when cyber threats are becoming more sophisticated. As a result, full network visibility is needed "like air" to monitor, manage and protect your network. Accessing data in flow down to the packet level is the first step to gaining full network visibility because nothing else provides a similar level of depth and granularity. Two of the most common methods to obtain this information are SPAN and TAP technologies.
In this article we will look at the specifics of traffic access via TAP and SPAN, some fundamental considerations, best practices, requirements and filter out some of the misinformation about SPAN or traffic access via switches. And also show that using TAP is the only viable and reliable technology 99% of the time.
SPAN or TAP? Here's the question!
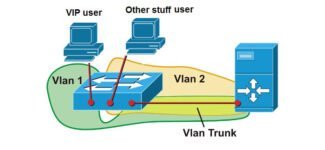
TAP (Test Access Point) and SPAN (Switch Port Analyzer or Switch Port for Analysis) technologies provide direct access to the actual packets moving across networks, but which methodology is preferable for today's infrastructures? If both work, when should you use TAP and when should you use SPAN? That is the question!
Until the early 1990s, most LAN analyzers were attached directly to the network to monitor it. Later, when hubs were used in network architecture, it became easier to analyze traffic. It was enough to connect the monitoring system to one of the ports of the hub, which allowed to receive every packet transmitted through the network.
As switches and routers evolved, and as a result of the abandonment of hubs, the technology that we know as the SPAN/Monitoring port of the switch emerged. Since then, the need to connect monitoring tools directly to the network disappeared, engineers began to use the SPAN port and direct "mirror" traffic from the switch or router to monitoring and information security devices.
By definition, the presence of a SPAN on a switch typically indicates the ability to mirror traffic from any or all ports to one unused port, but at the same time prohibits bidirectional traffic on that port to protect against the backflow of traffic into the network. SPAN technology was originally developed as a test point of quality assurance and quality control (debugging) devices for the network equipment manufacturers themselves, and the access point to the "mirror" traffic was implemented as a belated idea.
The main considerations regarding the requirements for full visibility of the real network
During any network deployment, there are many different factors that affect connectivity strategy and design. We've generated for you a checklist of key items to help you weigh the pros and cons when choosing a way to provide full network visibility.
Moment one: the "spy" mirror
A friend who works in a large hotel told me that many hotels have rooms with two-way mirrors. Of course, such "mirror spies" are not installed in all rooms, only in some.
The reason for their installation is simple – concern for safety. If there are doubts or suspicions about a guest, they try at all costs to put him in a room equipped with "mirror spies.

Agree, rarely would anyone want to live in a room that is, in fact, the site of a reality show. There are a couple of ways to check the mirrors built into the walls. That is, those under which it is impossible to look.
The first method involves using your own mirror. It is necessary to put it on a large mirror. You can fix the position with the help of double-sided adhesive tape. The essence of the test is to compare the reflections. If the reflection in the large hotel mirror is less clear, more muted than in your own mirror – you live in a room with a "spy".
The second way to check is to place your finger close to the surface of the mirror. You need to rest your fingernail against the glass and look at an angle, a little from the side. If there is a distance between the fingertip and its reflection – then everything is OK, the mirror on the wall is simple. But if the reflection is blurred, there are no clear boundaries and it is not clear whether there is a distance – there is a "spy" on the wall.

What to do in such a situation? It makes no sense to clarify the relationship with the employees. Go down to the lobby, gather more newspapers and magazines, go up to the room and cover the surface of the mirror.
Moment two: hidden cameras in rooms
Administrators at most hotels with video surveillance systems claim that there are no cameras in the rooms. But is it true?
Imagine you are a security officer and you need to identify a potential threat in time. Would cameras in corridors, elevators and in the lobby help you? Of course not. Unless you have "X-ray vision" and other superhero talents, you will never know what is in the guests' suitcases.
Accordingly, video cameras in the rooms are necessary for security. And, of course, they are there. Miniature hidden cameras are installed in hotel rooms. Typically, they are placed in places where you can get the best view and a clear picture and where, of course, curious guests will not look.
It is impossible to detect such cameras when visually inspecting the room. However, even a thorough search will not give anything. For example, you wouldn't dismantle the ceiling panels of the hotel room or break a nice decorative statue, would you?
However, it is still possible to find out if there are hidden video cameras in the room. An ordinary smartphone will help to find this out. It is necessary to shut the windows tightly, turn off the light and turn on the smartphone. The screen emits a faint blue glow, in which you can see the points of light projected by the "scope" of the video cameras.
Unfortunately, even if you calculate the trajectory of the camera's aim and understand where it stands, close this area – not the fact that you get rid of the surveillance of yourself. In such a situation, you just need to move to another hotel.
Causes of interference with the WI-FI signal
- Background operation of electrical appliances (microwave oven, boiler, air conditioner). To eliminate the problem, it is sufficient to remove the router from the source of interference.
- Interior objects in the signal path. For example, a new mirror or a massive cabinet may well become an obstacle between the router and the PC. Therefore, determine when the problems began and remove the unnecessary objects.
- Incorrect positioning of the antennas on the router. For example, if the router is installed in a closet in the hallway, you could accidentally hit the elements. Check that the center antenna is installed at a 90° angle and the side antennas are installed at a 45° angle.
If, despite the measures taken, the signal quality has not improved, the problem may be caused by outdated router software. In this case it is worth trying to update the firmware. If this fails, it remains only to change the equipment.
8 Ways to Strengthen the WI-FI Signal from the Router
If you have already figured out how to hide the router in the hallway or another room, it's time to try to strengthen the signal from the router.
- Set the optimal data frequency. This figure depends on the total area of the apartment, the size of each room, the number of rooms. Looking for a suitable mode should be in the settings of the router.
- Increase the signal transmission power. If there is such an option in the settings of your router. Power can be specified as a percentage or with the words High, Medium, Low.
- Change the signal mode. That is, the standard of the wireless network. However, it is important that the receiving device supports the desired mode.
- Switch to another broadcast channel. If the router is on the same wave as most of the neighbor routers, the signal quality will definitely not be too high. So try looking for a relatively free channel in your settings.
- Use amplifiers .. For example, boosters (Range Extender Booster). And you can also install additional antennas on the router.
- Replace the antennas.. If your device has removable elements, you can install more powerful parts. This will help increase the range of the network.
- Install repeaters. While boosters help extend the signal range, these devices are effective specifically for amplification. This is a good option when you need broadcast stability.
- Connect another router .. This option is suitable if other ways did not help to strengthen the signal. Or you have a large apartment. You can connect the second router with a special cable or via wi-fi. Just make sure that the settings of the devices specify different broadcast channels. Otherwise, instead of signal amplification, you will get thorough interference.
Important! New models of routers are perfectly controlled with the remote control. Such devices are easier to configure in the desired operating mode.
Read More: