Seoul Metro.
- Occupational Safety and Health Specialist
- Organization of Librarian Activities in Professional Education
- Features of the preparation for the General State Exam in Physics in the implementation of the FSES LLC
- Pedagogical activity on the design and implementation of the educational process in general educational organizations (subject "Physics")
- Slide 7 History There are only two ways to get rid of wires – to transmit information
- Slide 8 Iron Back
- Presentation Slides
- List of similar presentations
- Protecting your own information from unauthorized access
- Protecting your own information from unauthorized access
- Protecting your own information from unauthorized access
- Protection of information from unauthorized access.
- Protection of one's own information from unauthorized access
Occupational Safety and Health Specialist
To this discount we can add a discount for your educational institution (it depends on how many of your colleagues have attended Inforourock courses)
At the moment there are 56.586 educational institutions that have accumulative discounts (from 2% to 25%). To find out what discount is available to all employees at your institution, log in to your personal Infowalk account.


Organization of Librarian Activities in Professional Education
We can add your educational institution's discount to this discount (it depends on how many of your colleagues have completed the InforoLibrary courses)
There are currently 56,586 additional cumulative discounts (2% to 25%) available to 56,586 educational institutions. To find out which discount applies to all employees of your educational institution, log in to your personal "Infowalk" account.


Features of the preparation for the General State Exam in Physics in the implementation of the FSES LLC
To this discount we can add a discount for your educational institution (it depends on how many of your colleagues have completed the courses "Inforourock")
At the moment additional cumulative discounts (from 2% to 25%) are given to 56.586 educational institutions. To find out what discount is available for all employees at your educational institution, log in to your personal Infowalk account.


Pedagogical activity on the design and implementation of the educational process in general educational organizations (subject "Physics")
We can add a discount for your educational institution to this discount (it depends on how many of your colleagues have completed the Inforourock courses)
At the moment there are 56.586 educational institutions that get cumulative discounts (from 2% to 25%). To find out what discount is available for all employees of your educational institution, log in to your personal "Infowalk" account.


Slide 7 History
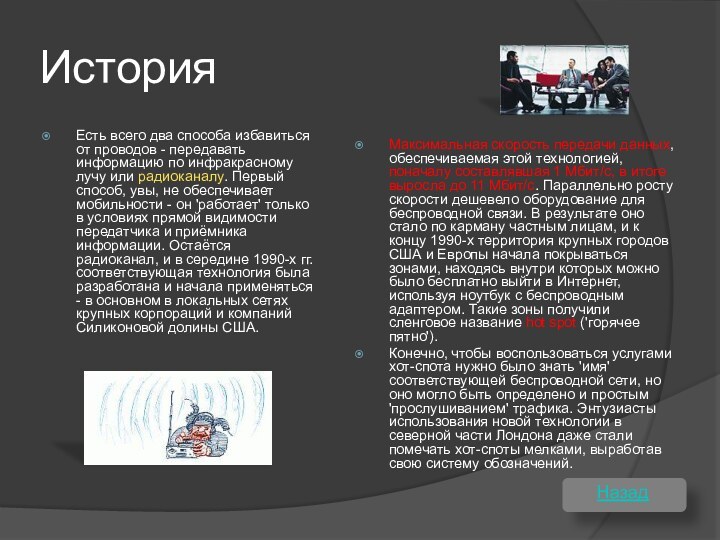
There are only two ways to get rid of wires – to transmit information
by infrared or by radio. The first way, alas, does not provide mobility – it 'works' only when the transmitter and receiver of information are directly visible. The radio channel remains, and in the mid-1990s the corresponding technology was developed and began to be used – mainly in the local networks of large corporations and companies in the Silicon Valley of the USA.
The maximum data transfer rate provided by this technology, which was initially 1 Mbit/s, eventually grew to 11 Mbit/s. In parallel with the speed increase, wireless equipment became cheaper. As a result the individuals could afford it, and by the end of the 1990s the territory of big cities of the USA and Europe began to be covered by zones inside which one could get to the Internet for free with a notebook with a wireless adapter. Such zones were given the slang name of a hot spot.
Of course, in order to use the services of a hot spot you had to know the 'name' of the respective wireless network, but it could also be determined by simply 'sniffing' the traffic. Enthusiasts of the new technology in North London even began to mark hot spots with crayons, developing their own system of labeling.
Back
Slide 8 Iron
Back

The wireless networking support in a laptop that doesn't come equipped with it by default. They have a built-in antenna, are compact and easy to set up.

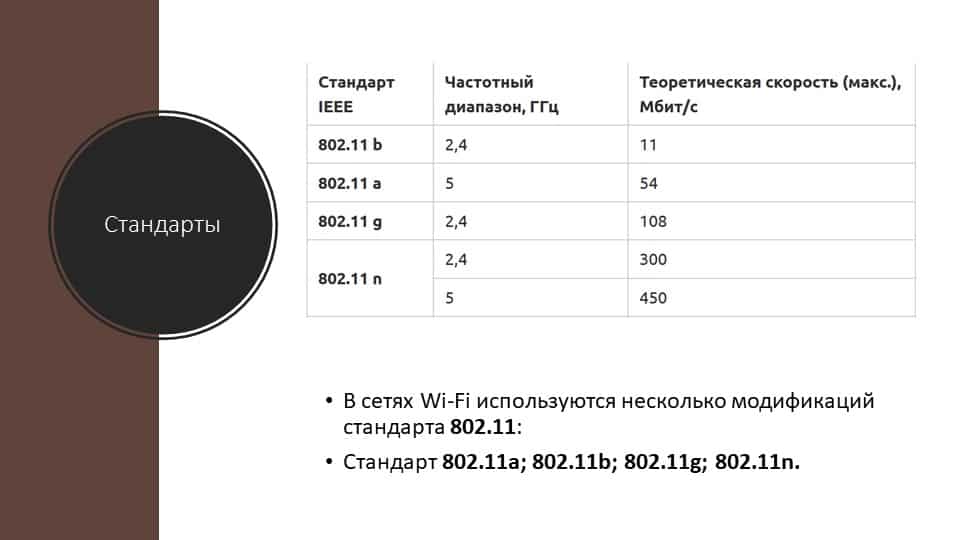
Wireless Cardbus adapter 802.11g, up to 108 Mbps
Presentation Slides


Wireless networking is an important part of almost any modern enterprise. With a fast, secure network, you can dramatically increase your productivity.

Wi-Fi is a system, usually covering tens of meters, that uses unlicensed frequency bands to provide network access. Usually Wi-Fi is used by users to access their own local network, which may not be connected to the Internet.


A WiFi wireless access point is a radio transceiver that connects wireless and wired devices into a local area network.

List of similar presentations
Protecting your own information from unauthorized access
Relevance. This topic is especially relevant today during the rapid development of computer technology. Because of the theft of sensitive data, many .

Protecting your own information from unauthorized access
Rule One. It is very important to come up with a good social media password, which will consist of a set of letters and numbers Examples: A)123456-bad B)Novo-sadovaya56 .
Protecting your own information from unauthorized access
Keeping your antivirus up to date and skillful user action is the minimum likelihood of unauthorized access. – Surfing the Internet.

Protection of information from unauthorized access.
protection from unauthorized access [protection from unauthorized access, fetch protection]. A complex of organizational, software and hardware.

Protection of one's own information from unauthorized access
The problem of protection of information from unauthorized access arose from the time when people for whatever reason did not want to share it with anyone or .
Read More:





