802.11ax delivers greater efficiency and security than previous versions of the protocol. Its theoretical maximum transfer speed is about 10 Gbps—30 percent faster than Wi-Fi 5. 802.11ax is backward compatible with the other protocol versions.

Wireless Networking Protocols Explained
Tony Bradley is a former Lifewire writer and tech journalist who specializes in network and internet security. He is a respected information security expert and prolific author.
In This Article
A protocol is a set of rules or agreed-upon guidelines for communication. When communicating, it is important to agree on how to do so. If one party speaks French and one German, the communications will most likely fail. If they both agree on a single language, communications will work.
The 802.11 family of wireless networking protocols is the standard for wireless networking and makes it possible for devices to interact.

Wireless Networking Protocols
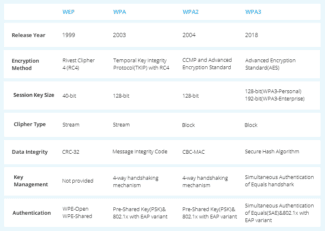
TCP/IP is a collection of protocols that each have their own particular functions or purpose. These protocols were established by international standards bodies and are used in almost all platforms worldwide so that all devices on the internet can communicate successfully. The 802.11 wireless networking protocols have gone through several iterations, each one surpassing the previous version in capability and speed.
Not all equipment functions with every version, so it's important to know which protocol version your equipment uses. In general, newer equipment supports the most recent of the protocols, and older equipment may not. Typically, equipment supports multiple protocols. For example, equipment tagged 802.11ac/n/g is compatible with three protocols.
What are communication protocols?
A communication protocol is a list of unified instructions that specify how certain software or hardware interfaces should handle the transfer of data – for example, text, graphics, audio and video streams. Relevant protocols are created primarily to facilitate the scaling of various computer networks. For example, the introduction of TCP/IP unified data transmission virtually worldwide, making it possible to integrate computers into the global network of the Internet.
In today's market of information technology, communication channel protocols are used at the most different levels of implementation of communication interfaces. They are constantly being refined, updated. From time to time new protocols are developed, reflecting the specifics of the development of the communication market. Various communication protocols can be used in both domestic and industrial networks, implemented on the infrastructure of research centers, etc. Among the most common standards of the relevant type are Ethernet, CAN, HART.
The use of communication protocols is also carried out in the sphere of mobile communication services. Among them are 3G, 4G and GPRS.

These protocols in the networks of mobile operators differ, in particular
– in the rate of data transmission between the subscriber and the provider of communication services;
– in terms of the maximum distance of the communication device to the base station.
As for the classification of computer communication protocols – it is characterized by a fairly high level of complexity. Let's consider its specifics in detail.

Classification of computer communication protocols
The classification of the relevant protocols can be done using a fairly large number of approaches. A common one is the one in which communication standards can be subdivided into lower and higher levels. These include:
The level under consideration, within which a particular communication protocol can be classified, refers primarily to applications. That is, it provides communications between the network infrastructure and specific user programs. Protocols such as HTTP, Telnet, DNS, IRC, BitTorrent and many others are used here, through which modern online services are delivered.
Threats of wireless technologies
Significant security problems of wireless networks, despite their significant pluses, is one of their main drawbacks. In this respect, they are much inferior to a wired connection. This is due to the fact that to break into a wired network an intruder needs direct access to the cable, which is much more difficult to obtain than intercepting the radio signal with special devices. Moreover, wireless networks often operate without even basic password protection.
Gaining access to the local wireless network provides hackers with a way to steal confidential information and personal data, spread malware, for other manipulations.
There are several basic types of attacks that threaten the security of wireless computer networks:
Each of these types can be used by hackers in certain environments with different objectives.
"Man in the middle."
"Man-in-the-Middle," or Man-in-the-Middle, is among the most common types of attacks. This method is most often used to connect to access points not protected by a password. Since the signal in such networks is transmitted without encryption, an intruder can easily intercept it using a normal laptop or computer with a Wi-Fi adapter. However, it is possible that a hacker can also connect to a password-protected network by using a special program to crack passwords by brute force.
Man-in-the-Middle attacks, in turn, are divided into two types – eavesdropping and manipulation.
"Eavesdropping is also called a passive attack. It is carried out with the help of special software, which after gaining access to the local network displays all the traffic of the user on the intruder's computer. This could be the history of sites visited, logins and passwords entered, credit card data and other sensitive information.
Manipulation attacks are called active attacks. In this case, the hacker is not only able to steal the user's personal data, but also to manipulate his device via the wireless network. For example, using special software, a command can be sent to the user's computer on behalf of the access point to redirect the browser to a specific page on the Internet. On that page, the computer becomes infected with viruses or other malicious software.
Security Recommendations
Securing wireless networks is quite a complex task. It is difficult because of the inability to physically isolate intruders from the network or trace their location. However, simple guidelines can go a long way toward insuring your network and minimizing the risk of an attack.
Top tips for securing wireless networks:
- Ensure that your network device is physically protected. The router must be installed in such a way as to prevent interference, e.g. from a microwave oven. Also the possibility of accidentally pressing the reset button must be eliminated.
- Change the default login and password. Data for access to the router's configuration interface and Wi-Fi network, are specified in the instructions for the device. It is recommended to change these data by creating a strong password.
- Deny broadcasting the network ID. In that case only the user who knows the network ID will be able to connect to your wireless network.
- Apply filtering by MAC address. Filtering can help limit the number of devices that can connect. It will only allow certain devices with the MAC settings to connect to the network. This measure will make it much more difficult for intruders to access the network and will help eliminate the possibility of "dummy" connections.
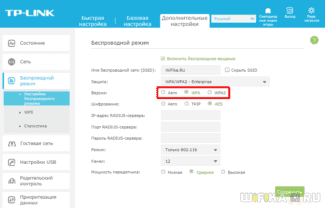
- Use effective wireless security protocols. For example, when setting up the router, it is recommended to set the security protocols to WPA/ WPA2.
- Use a firewall on your computer. A software firewall is installed by default on Windows systems starting with XP. Third-party firewalls can be used. A firewall provides control and filtering of traffic to protect against network threats. Therefore, such a company should always be active.
- Use an effective antivirus that is regularly updated.
- Limit the range of the network. Ideally, it is best to limit Wi-Fi coverage only to the confines of your apartment or office. This will make it impossible or very difficult for an intruder to physically access the wireless network.
- Deny access to the router settings via Wi-Fi. In this mode, changing the settings will require a cable connection, that is, physical access to the network device, which is not available to outsiders.
- Avoid using unsecured wireless networks in public places. It is also not advisable to connect to someone else's unprotected network within your home. This could be a false access point used by hackers to steal data.
- Always disconnect your router when you are not using the Internet. This measure will reduce the likelihood of being attacked.
- Use Bluetooth carefully. The feature should be turned off on your phone at all times. It is recommended that you only turn Bluetooth on immediately before using it. Reject connection requests from unknown devices and do not accept any files from them.