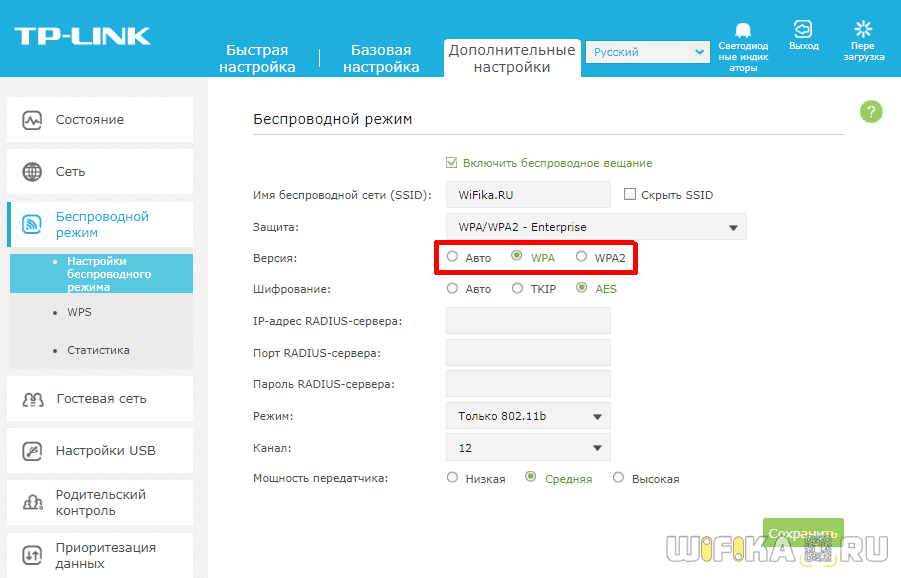
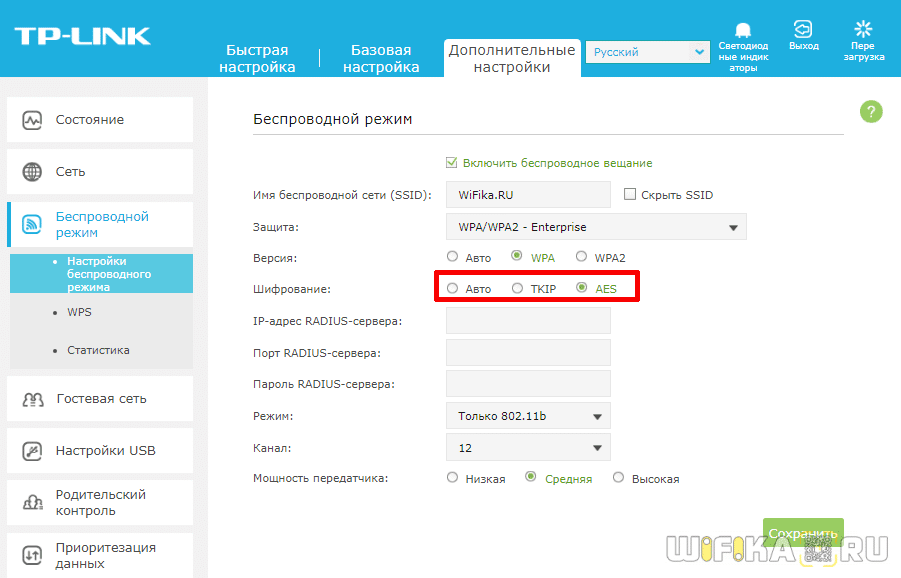
And this is how these security settings look like on TP-Link routers (with old firmware) .
- The type of wireless security and encryption. Which one to choose?
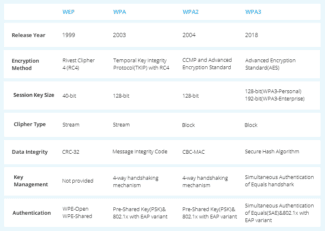
- Wi-Fi security: WPA3, WPA2, WEP, WPA
- WiFi data encryption and types of authentication
- What is WEP wifi security?
- What is a WPA key or password?
- What is WPA2-PSK – Personal or Enterprise?
- What is WPA3-PSK?
- WPA Encryption Type – TKIP or AES?
- EAP
- How reliable is this?
- Configuring the security of Wi-Fi routers and access points
- WPA3 – The largest Wi-Fi security update in 14 years 8
- The new authentication mechanism is SAE (Simultaneous Authentication of Equals)
- Pass me the sugar
- Plan of attack
- Creating a complex password
- Vulnerability
- How to crack WPA2-PSK?
The type of wireless security and encryption. Which one to choose?
In order to protect your Wi-Fi network and set a password, you must necessarily choose the type of wireless network security and encryption method. And at this point many people have a question: which one should I choose? WEP, WPA, WPA2, or WPA3? Personal or Enterprise? AES, or TKIP? What security settings will best protect your Wi-Fi network? In this article, I will try to answer all of these questions. Let's take a look at all of the authentication and encryption methods that are available. Let's find out what Wi-Fi network security settings are better to set in the router settings.
Note that security type, or authentication, network authentication, security, authentication method are all the same thing.
Authentication type and encryption are the basic settings for securing a wireless Wi-Fi network. I think to begin with we need to understand what they are, what versions there are, their capabilities, etc. After that we will figure out what type of security and encryption to choose. I will show you an example of some popular routers.
I strongly recommend that you set up a password and protect your wireless network. Make it as secure as possible. If you leave your network open and unsecured then anybody can connect to it. This is not very secure in the first place. As well as the unnecessary load on your router, connection speeds drop and all sorts of problems with the connection of various devices.
Wi-Fi security: WPA3, WPA2, WEP, WPA
There are three security options. Of course, not counting "Open" (No protection) .
- WEP (Wired Equivalent Privacy) is an outdated and insecure method of authentication. It is the first and not a very good security method. Attackers have no problem accessing wireless networks that are protected with WEP. You do not need to set this mode in your router's settings, although it is there (not always).
- WPA (Wi-Fi Protected Access) – reliable and advanced type of security. Maximum compatibility with all devices and operating systems.
- WPA2 – Improved and more secure version of WPA. There is support for AES CCMP encryption. This is the current version of the protocol, which is still used on most home routers.
- WPA3 – is a new standard that allows for greater protection against attacks and provide stronger encryption than the previous version. OWE encryption also increases the security of public open networks. It was introduced in 2018 and is already actively used in almost all modern routers and clients. If your devices support this version, use it.
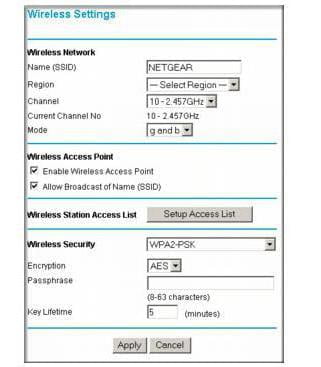
- WPA/WPA2 – Personal (PSK) – is a common authentication method. When you only need to set a password (key) and then use it to connect to the Wi-Fi network. One password is used for all devices. The password itself is stored on the devices. Where it can be viewed or changed if necessary. It is recommended to use this option.
- WPA/WPA2 – Enterprise – A more sophisticated method used mainly for securing wireless networks in offices and institutions. It provides a higher level of security. It is only used when a RADIUS server (which issues passwords) is installed for device authentication.
WiFi data encryption and types of authentication
So, we have seen the need for wifi network encryption, now let's see what types there are:
What is WEP wifi security?
WEP (Wired Equivalent Privacy) is the very first standard that appeared, which in terms of reliability no longer meets modern requirements. All programs set up to break into the wifi network by brute forcing are mainly aimed at finding the WEP encryption key.
What is a WPA key or password?
WPA (Wi-Fi Protected Access) is a more modern standard of authentication that allows you to reliably protect your local network and the Internet from illegal intrusions.
What is WPA2-PSK – Personal or Enterprise?
There are two other security standards for WiFi WPA2 and WPA:
- Personal, referred to as WPA/PSK or WPA2/PSK. This type is the most widely used and is best for most purposes – at home or in the office. With WPA2/PSK, we set a password of at least 8 characters, which is stored in the memory of the device that we connect to the router.
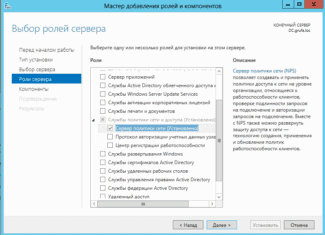
- Enterprise is a more complex configuration that requires RADIUS enabled on the router. It works like a DHCP server, i.e. a separate password is assigned for each individual connected gadget.

What is WPA3-PSK?
The standard of WPA3-PSK encryption has appeared quite recently and has come to the replacement of WPA2. Although WPA2 is known for its high security features, WPA3 is not vulnerable to being hacked. All modern devices already support this type – routers, access points, wifi adapters, and others.
WPA Encryption Type – TKIP or AES?
So, we have decided that WPA2/PSK (Personal) is the best choice for network security, but it has two other types of encryption for authentication.
- TKIP – this is an obsolete type today, but it is still widely used because many devices for a number of years now only support it. Does not work with WPA2/PSK and does not support 802.11n WiFi.
- AES is the latest and most secure type of WiFi encryption.
EAP
- EAP-FAST (Flexible Authentication via Secure Tunneling) – developed by Cisco; allows authorization by a login-password sent inside a TLS tunnel between a supplicant and a RADIUS server
- EAP-TLS (Transport Layer Security). Uses a public key infrastructure (PKI) to authenticate the client and server (supplicant and RADIUS server) through certificates issued by a trusted certificate authority (CA). Requires the issuance and installation of client certificates on each wireless device, so it is only suitable for a managed enterprise environment. The Windows Certificate Server has the means to allow the client to generate its own certificate if the client is a domain member. Blocking a client is easily done by revoking its certificate (or through accounts).
- EAP-TTLS (Tunneled Transport Layer Security) is similar to EAP-TLS, but does not require a client certificate. In this tunnel, which is similar to an SSL browser connection, there is additional authorization (by password or something else).
- PEAP-MSCHAPv2 (Protected EAP) – is similar to EAP-TTLS in terms of the initial establishment of an encrypted TLS tunnel between the client and the server that requires a server certificate. This tunnel is then authenticated using the well-known MSCHAPv2
- PEAP-GTC (Generic Token Card) – similar to the previous one but requires one-time password cards (and corresponding infrastructure)
All these methods (except EAP-FAST) require a server certificate (on the RADIUS server) issued by a Certificate Authority (CA). The CA certificate itself must be present on the client device in the trusted group (which is easy to implement by means of group policy in Windows). Additionally, EAP-TLS requires an individual client certificate. Client authentication is verified either by digital signature or (optionally) by comparing the certificate provided by the client to the RADIUS server with the one that the server retrieved from the PKI-infrastructure (Active Directory).
How reliable is this?
After all, what does it take for an attacker to break into your network?
For Open Authentication, No Encryption, nothing. Connected to the network, and that's it. Since the radio environment is open, the signal spreads in different directions, it's not easy to block it. With the proper client adapters that allow you to listen to the air, the network traffic is visible as if the attacker connected to the wire, to the hub, to the SPAN port of the switch.
WEP-based encryption requires only the time to try the IV, and one of the many scanning utilities freely available.
For encryption based on TKIP or AES, direct decryption is theoretically possible, but in practice there have been no cases of breaking.
Of course, you can try to pick up a PSK key, or a password to one of the EAP-methods. Widespread attacks on these methods are not known. It is possible to try social engineering methods, or thermorectal cryptanalysis.
Gaining access to a network protected by EAP-FAST, EAP-TTLS, PEAP-MSCHAPv2 is possible only when the user's login and password are known (hacking as such is not possible). Attacks such as brute force password attacks or attacks targeting vulnerabilities in MSCHAP are also not possible or are difficult because the EAP "client-server" channel is protected by an encrypted tunnel.
Access to a network closed by PEAP-GTC is possible either by hacking the token server or by stealing the token along with its password.
Access to a network closed by EAP-TLS is possible if the user's certificate is stolen (along with its private key, of course), or if a valid but fake certificate is issued. This can only happen if the CA has been compromised, which normal companies treat as their most valuable IT resource.
Since all of the above methods (except PEAP-GTC) allow for saving (caching) passwords/certificates, when a mobile device is stolen, the attacker gets full access without asking too many questions from the network. A preventive measure could be full encryption of the hard drive with a password prompt when the device is turned on.
Configuring the security of Wi-Fi routers and access points
Many people today have a Wi-Fi router at home. It is much easier to connect a notebook, tablet or smartphone to the Internet without a wireless connection, and there are more such devices in every family than there are people. And it (the router) is essentially the gateway to the information universe. Read the front door. And that door determines whether or not an intruder comes in without your permission. So it is very important to pay attention to the proper configuration of the router so that your wireless network is not vulnerable.
I don't need to remind you that hiding the access point's SSID does not protect you. Restricting access by MAC address is not effective. Therefore, only modern encryption methods and a strong password.
WPA3 – The largest Wi-Fi security update in 14 years 8
In 2022 a serious vulnerability named KRACK (Key Reinstallation Attack) was found in the WPA2 protocol. This fact, along with all the previously known shortcomings of WPA2, prompted the Wi-Fi Alliance to develop a new security standard – WPA3.
Wi-Fi has long been an integral part of the lives of millions of people, and with the emergence of IoT the number of wireless devices around the world is constantly growing, so the issues of Wi-Fi network security do not lose their relevance. The previous version of the protocol WPA2 was introduced in 2004 and over the past few years has been repeatedly discredited. For this reason, in July 2022, the Wi-Fi Alliance announced the certification of devices supporting WPA3 (Wi-Fi Protected Access 3) – the largest security update in 14 years.
The new authentication mechanism is SAE (Simultaneous Authentication of Equals)
With WPA2, the use of weak passwords has always been a critical issue. If users put an easy password on a wireless network, it could easily be guessed by automated dictionary attacks, such as Dictionary and Brute-Force. The WPA2 protocol never offered options to solve this problem. The only recommendation from the developers was to use complex and more secure passwords. WPA3 will take measures to counter such attacks.
For this purpose, a new SAE (Simultaneous Authentication of Equals) authentication mechanism has been implemented in WPA3, which replaces the PSK (Pre-Shared Key) method used in WPA2. It is PSK that describes a four-step handshake to establish communication. This method has been compromised by the KRACK attack, which interrupts a series of handshakes and attempts to repeat the connection request. Repeatedly sending greeting messages forces network participants to reset an already agreed upon key. When the victim resets the key, the associated parameters are reset, compromising the security that WPA2 is supposed to guarantee. Thus, the attacker is able to listen to traffic and inject their packets.
Pass me the sugar
Imagine that you are a device that receives instructions. Anyone can connect to you and give you any command. Everything is fine, but at some point you have to filter out the personalities who can control you. This is where the fun part comes in.
How do you figure out who can give a command and who can't? The first thing that comes to mind is by password. Have each client give some kind of password before giving a new command. That way, you will only execute commands which were followed by the correct password. The rest are screwed.

That's how the HTTP basic authorization (Auth Basic) works:
AuthType Basic AuthName "My super secret zone!" AuthUserFile /home/.htpasswd Require valid-user 
After successful authorization, the browser will just pass a certain header on every request to the closed zone:
This approach has one big disadvantage – since the password (or login-password, which is essentially just two parts of the same password) is transmitted over the channel "as is" – anyone can get in between you and the client and get your password on a platter. And then use it and dispose of you however they want!
To prevent this nuisance, you can resort to a ruse: use some two-way encryption algorithm, with our password as a private key, and never share it explicitly. However, this will not solve the problem – it is enough to know the password once and you can decrypt any data transmitted in the past and in the future, plus encrypt your own and successfully masquerade as a client. Considering that the password is intended for a human and that people are not inclined to use the entire 256-byte set of symbols, and that these symbols are usually about 6-8… well, the Komsomol will not approve.
Plan of attack
Attentive readers, of course, have noticed that no matter how cunning we are, we can't get away from transmitting the password and the temporary key in plain or hashed form. As a result, all a hacker needs to do is intercept the transmission at this phase, and he can read all the subsequent data and participate in the process by inserting his five kopecks. And it is impossible to tell the difference, because all the information that would guide the server for issuing a temporary key or access verification is based exactly on what was at the beginning of the transmission – the handshake. So the hacker knows everything the server and the client know, and can fool both until the temporary key expires.
Our job in hacking any transmission somehow comes down to intercepting the handshake, from which we can either pull the temporary key, the original password, or both. All in all, it's a pretty long undertaking and requires a certain amount of luck.
Creating a complex password
To create a complex password, the conditions must be met:
- Length: the more characters in the combination, the harder it is to pick, even by software.
- Complexity: a strong password includes letters of different case and numbers. Spaces, dashes at the bottom and complex symbols are not suitable because they are difficult to enter, especially on mobile devices or Smart TV sets.
- Common phrases, names, and dates should not be used – such passwords are easy to pick.
By following these simple rules, you can be sure that your network cannot be hacked by intruders.
A network security key is a sequence of numbers, letters and symbols that protects access to Wi-Fi. If you forget it, you can view it on your PC, laptop, smartphone, or router. The password can be edited or deleted by resetting the router to its initial settings. When entering a new code, keep in mind: the more complex it is, the more secure the wireless connection will be, and therefore the harder it will be for intruders to break it.
Vulnerability
Back in 2008 at the PacSec conference there was a presentation which made it possible to hack the wireless connection and read the data coming from the router to the client terminal. All this took about 12-15 minutes. However, it was not possible to hack the backhaul (client-router).
The thing is that when the router's QoS mode is on, not only can the transmitted information be read, but it can also be replaced by fake one. In 2009, Japanese specialists presented a technology that allows to reduce the break-in time to one minute. And in 2010 information appeared on the web that it is easier to crack the Hole 196 module, present in WPA2, by using your own private key.
There is no question of tampering with the generated keys. First, a so-called dictionary attack is used in combination with a "brute-force" attack, and then the wireless connection is scanned in order to intercept transmitted packets and then record them. Once the user connects, it is immediately de-authorized, intercepting the initial packet transmission (handshake). After that even being close to the main access point is not required. You can safely work offline. However, all these actions will require special software.
How to crack WPA2-PSK?
For obvious reasons, a full algorithm of connection hacking will not be presented here, as it can be used as a kind of instruction for action. Let's focus only on the main points, and only in general terms.
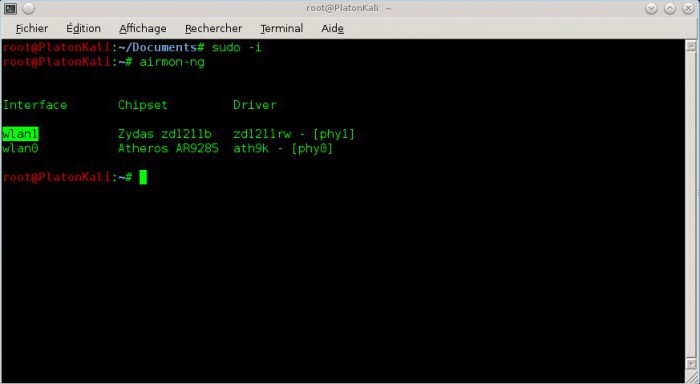
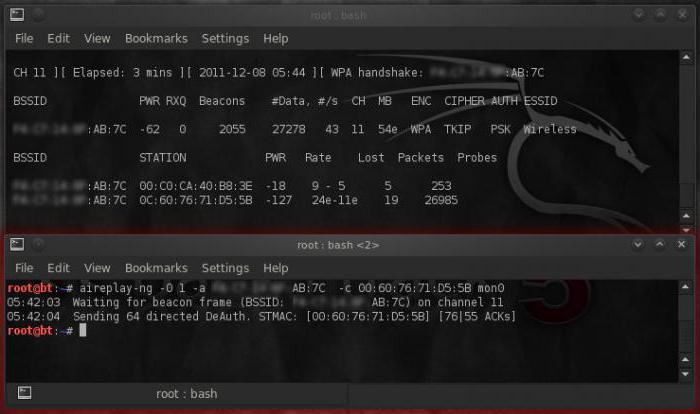
As a rule, when directly accessing the router, it can be put into the so-called Airmon-NG mode for traffic tracking (airmon-ng start wlan0 – renaming the wireless adapter). After that traffic is captured and fixed using airdump-ng mon0 command (channel data tracking, beacon speed, speed and encryption method, amount of transmitted data, etc.).
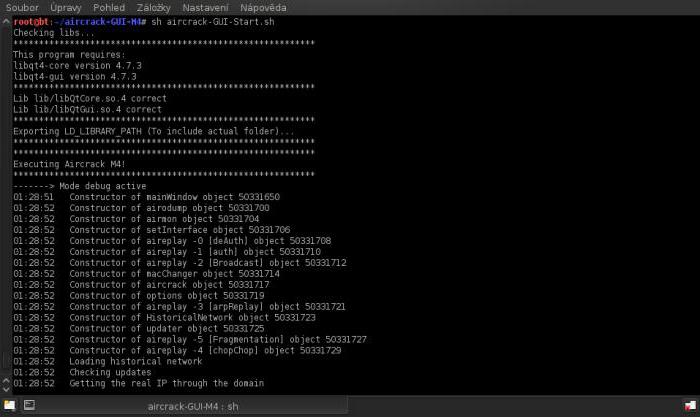
Next, the command to commit the selected channel is invoked, after which the Aireplay-NG Deauth command is entered with the accompanying values (they are not given for reasons of legality of using such methods).
After that (when the user is already authorized to connect), the user can simply disconnect from the network. In this case, when the intruder logs in again, the system will reauthenticate the login, after which all the access passwords can be intercepted. Next, a "handshake" window will appear. Then, you can run a special WPAcrack file, which will allow you to crack any password. Naturally, no one is going to tell you how to run it. It should be noted only that the entire process takes from several minutes to several days, provided you have some knowledge. For example, a processor of Intel level operating at standard clock frequency of 2.8 GHz is able to process not more than 500 passwords per second, or 1.8 million passwords per hour. All in all, as is already clear, don't get your hopes up.
Read More: