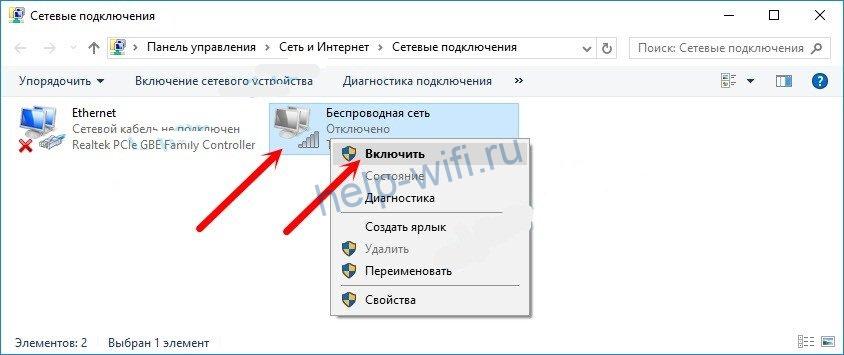
You can try to enable the adapter through "Network Connections" by selecting the appropriate item in the context menu.
- How to find a Wi-Fi device with a directional antenna
- Why look for Wi-Fi signal
- A bit of theory
- The general network layout
- Activating Wi-Fi adapter on an Asus notebook
- The switch or a combination of buttons on the keyboard
- Without Fn key
- Using BIOS
- Installing drivers
- Advantages and disadvantages of Wi-Fi
- How to set up a wi-fi network in your home
- How to connect a router
- How to get into a router
- Setting up Wi-Fi the first time you turn it on
- The router indicators are the most useful information for configuration and use
- Closed Wireless Network
- Connecting to a closed wireless network on Windows 8 and earlier devices
- Aircrack
- Reaver-wps
- How the "jammer" works
- WARNING
- Real time monitoring with NetSpot
- Looking for APs with weak protection and determining the direction to them
- Exterior Examination
- News from the morgue
How to find a Wi-Fi device with a directional antenna
If, for example, you suspect your neighbor of connecting to your Wi-Fi network and can't be sure of your guesses, the above technique can help in gathering evidence.
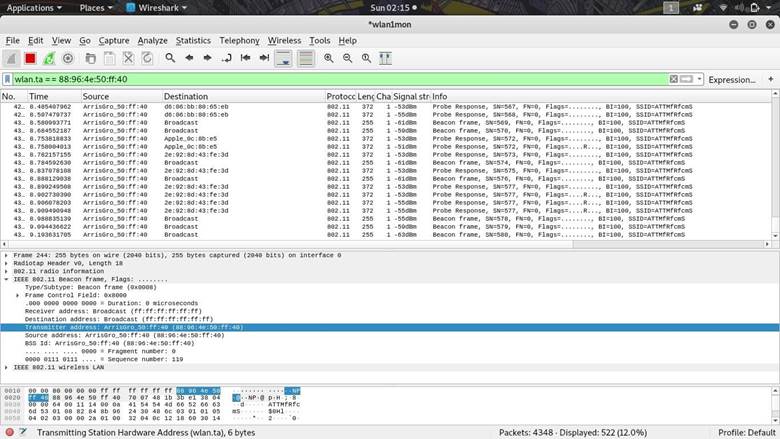
Author: Kody If you've ever wondered about tracking the source of a Wi-Fi signal transmission, the task is relatively easy with the right equipment. For example, with a directional Wi-Fi antenna and Wireshark, we can create a screen filter for any target device that is in the available range in order to plot signal strength. By moving the antenna in different directions, we can easily detect the direction the signal is coming from by observing the power peaks on the graph.
Why look for Wi-Fi signal
If you've ever observed someone else's Wi-Fi network, you've probably wondered if you can figure out where the signal is coming from. The source of that signal could be a suspicious access point that has appeared near your workplace, or a new network with a strong signal near your home, or a hotspot from a smartphone that seems to be high-powered and extremely close. In any of the above cases, signal search can help in detecting client Wi-Fi devices. Accordingly, you can track the location of malicious devices that suddenly appear on your wireless network. The idea of tracking radio signals is nothing new, but for the novice researcher who wants to locate the source of a Wi-Fi network, the possibilities may initially seem limited. Walking around a nearby area with a device (such as a smartphone) that displays signal strength, you can observe how you approach and move away from the broadcast source. However, this method is not accurate enough because the Wi-Fi signal is reflected by walls and other obstacles. The problem with this approach is the non-directional antenna, which has a pattern that looks like a donut. This pattern allows you to receive a signal from a nearby network in almost any direction, but it does not allow you to find the exact direction the signal is coming from. An alternative is to use an antenna with a narrow beam pattern, such as a Yagi, panel, or parabolic array. Unlike a doughnut shaped diagram, a directional antenna receives a stronger signal when pointed at a target.
When the task of visualizing signal strength in a visual form in order to track suspicious devices comes up, Wireshark comes in handy, as it is able to display the strength of the transmitted signal from all nearby Wi-Fi devices that we specify. Although this feature is not well documented, the process of identifying the target device and displaying signal strength graphically is surprisingly simple. In conjunction with a network adapter in monitoring mode and a Wi-Fi antenna with a narrow beam pattern, Wireshark will be able to quickly locate any Wi-Fi device within the available viewing radius. The signal search process in Wireshark is organized roughly as follows. First we switch the network adapter to monitor mode and start scanning for targets with the help of airodump–ng in order to detect the channel where the device in question is located. Once the appropriate channel our target is broadcasting from has been found, we can move on to scanning the specific channel to retrieve packets and display the resulting information in graphical form. Once anchored in the desired channel we can open Wireshark, find packets from the device we want to monitor and then create a screen filter to display only packets transmitted from the desired device. At the end of the process we try to find bursts using a graph which shows the signal strength as a function of time while moving the directional antenna.
A bit of theory
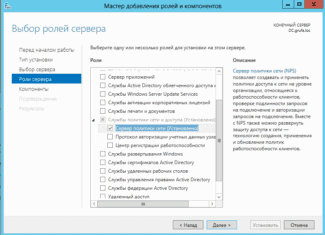
Some time ago the IEEE engineers came up with the 802.1x standard. This standard is responsible for the ability to authorize a user immediately when connected to a data environment. In other words, if you connect to a medium (a switch) for example PPPoE and you can already transfer data, authorization is needed to access the Internet. With 802.1x you cannot do anything unless you are authorized. The end device itself will not let you in. There is a similar situation with Wi-Fi access points. The decision to allow you is made on an external authorization server. This can be RADIUS, TACACS, TACACS+ etc.
- Open – available to all
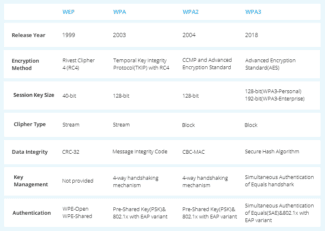
- WEP – old encryption. Everybody is so sick of the idea that it should not be used at all
- WPA – uses TKIP as the encryption protocol
- WPA2 – Uses AES encryption
There are also quite a few other ways to connect the endpoint to the authentication server (PEAP, TLS, TTLS. ). I will not describe them here.
The general network layout
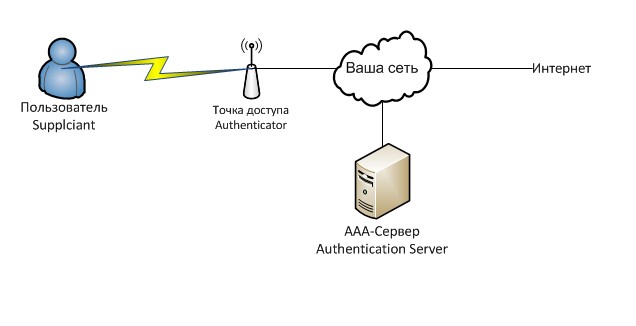
Here is the general layout of our future scheme for better understanding:
In words, the client, when connecting to the Wi-Fi – point is invited to enter a login and password. Upon receiving the login and password, the Wi-Fi hotspot transmits this data to the RADIUS server, to which the server answers what you can do with this client. Depending on the response, the point decides whether to give it access, reduce the speed or something else.
Our server with freeradius installed will be responsible for user authorization. Freeradius is an implementation of the RADIUS protocol, which is an implementation of the common AAA protocol. AAA is a set of tools to perform the following actions:
Authentication – checks the validity of login and password.
Authorization – checks that you have rights to perform certain actions.
Accounting – takes into account what you do in the system.
The protocol itself transmits the user name, a list of attributes and their values for him. That is, for example, Auth-Type attribute := Reject – to reject this client, and Client-Password == "password" – to compare the attribute in the request with the value of password.
Generally speaking, the database of accounts and their permissions don't necessarily have to be stored on the RADIUS-server, and the database can be anything – the Nix users, Windows domain users… even a text file. But in our case everything will be in one place.
Activating Wi-Fi adapter on an Asus notebook
The way to activate the wireless module depends on the laptop model. The Wi-Fi module can be turned on:
The switch or a combination of buttons on the keyboard
In the majority of Asus laptops the Wi-Fi module is activated by a combination of the Fn button and one of the keys (from F1 to F12). Most often it is Fn+F2. There is a special symbol on the desired button.

There are laptop models in which the special key is not on the keyboard, but above it.
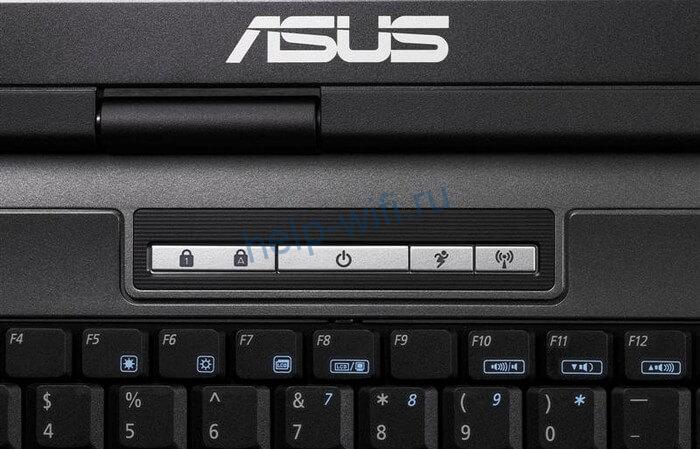
Older laptops have a special toggle switch to activate the wifi module. It is located on one of the side edges of the case or next to the touchpad.

Without Fn key
You can activate Wi-Fi without using the function buttons. To do so:
- In the tray, click on the wireless icon next to the clock.
- In the menu that opens, select "Network and Sharing Center".
- A window will open with a view of the network information. Click on "Change adapter settings".
- This will open a list of network connections. Click on "Wireless network" and select "Enable".
Using BIOS
If the device manager does not show a wireless network adapter, you need to restart your computer and go into the basic settings. On an Asus laptop, you must hold down the F2 key immediately after restarting.
In the bios, you need to find the section where the wireless interface settings are located. In older versions of the basic settings it is in the Security tab, under I/O Interface Security. If the Wireless Network Interface item is set to Lock, it must be changed to Unlock, save the changes and restart the laptop. After the restart, the WiFi must work.
Installing drivers
Laptop with a preinstalled operating system has a standard driver package by default. It ensures the correct operation of the components. But if the laptop didn't have an OS by default, you need to install the drivers. They are available on the disc that comes with the laptop, and on the official website of Asus.
You can install the drivers by booting from the disk. This method is suitable for laptops with a built-in optical disc drive.

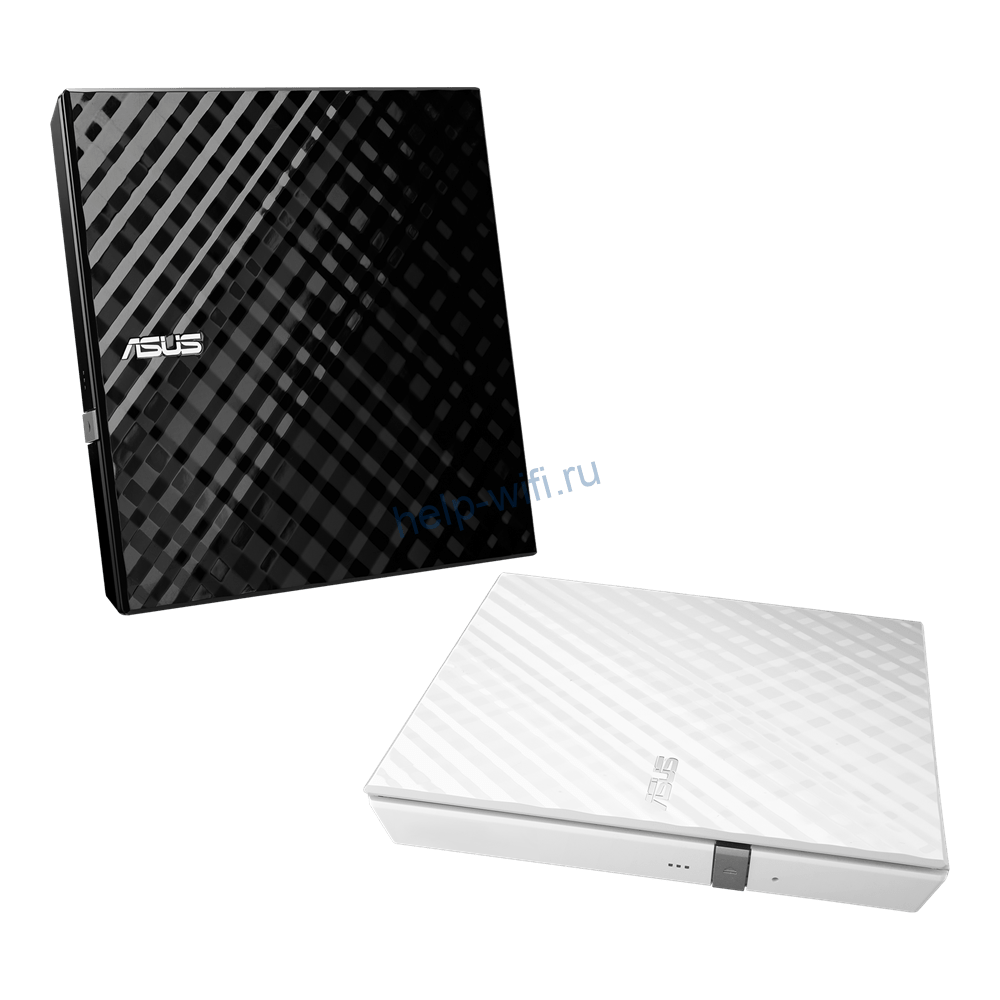
A disadv-rom missing in most newer models of laptops. But Asus has a series of portable dvd-drives for laptops.
The second way to install drivers is through the Device Manager. You need to save the files on your laptop beforehand. To find the driver, go to the official Asus website.

If you don't know the model of the laptop, look at the sticker on the back of the case.

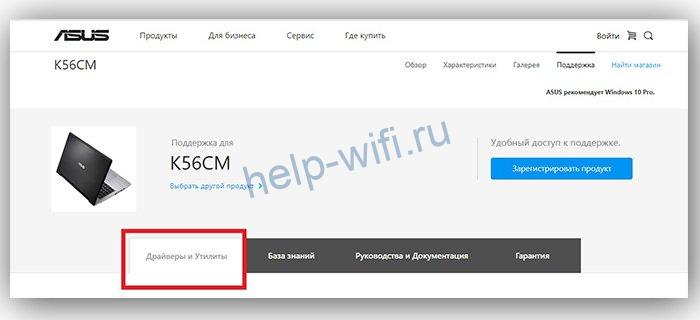
Once the search returns the laptop's page, go to the "Support" section.

Under "Support," open the "Drivers and Utilities" tab.
Advantages and disadvantages of Wi-Fi
Like any technology, wifi has pros and cons.
- Wireless networking (you can avoid tripping over wires);
- Coverage within 70 m is quite enough for household needs;
- One access point – many devices;
- Higher speed;
- If you connect your smartphone to wifi, your phone's battery lasts longer;
- Secure latest protocols.
- Network latency (relevant to gamers);
- Wi-Fi speed limitation – reduced speed of the user;
- "Natural" signal jamming at home;
- Interference with other devices at 2.4 MHz;
- Poor security of outdated security protocols.
How to set up a wi-fi network in your home
A router, or router, is the main way to set up a wi-fi network in your home. Below, let's look at all aspects of choosing a router and the tasks it will perform.

How to connect a router
First, the router itself needs to be connected to the Internet. This is done with special cables that can connect the router not only to your computer or laptop, but also a game console or TV set-top box.

How to get into a router
Once in the router, you can change the password, network name, configure the router or change its settings. To do this you need to open a special numeric IP address in the browser of your computer or phone and enter the username and password indicated on the back of the router. Often these are 192.168.1.1, or 192.168.0.1 and the same username and password are admin.

Important!
Login and password of the router are not data for connection to Wi-Fi network!
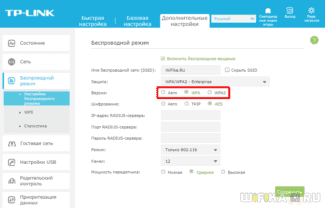
Setting up Wi-Fi the first time you turn it on
- In the same way, in the router settings, set the connection to the Internet with the login and password of the Internet service provider, the type of the necessary connection – PPPoE;
- then check the wireless connection option in the router settings;
- Set a unique name for your network.
Interesting!
You can leave the network name "MGTS_GPON_5752", or rename it to "Home" or create your own exotic variant.
In the future, this network will be connected to the router and all other devices.
The router indicators are the most useful information for configuration and use
There are several indicators on the router that convey valuable information about the status of the device and connection:
Closed Wireless Network
Connecting to a closed wireless network is done differently for each operating system:
The first time you connect to a wireless network using your Android mobile devices, follow these steps:
- Select the "Study" network from the list of available networks and tap "Connect";
- In the window that opens (Fig. 2), select:
- EAP-PEAP Method.
- Authentication step 2 – MSCHAPV2
- Authentication/Username – your login
- Password – your personal password
Figure 2: Connecting to a closed Wi-Fi network (Android OS)
Connecting to a closed wireless network on Windows 8 and earlier devices
If you are connecting to a wireless network for the first time with devices running Windows 8 or earlier, follow these steps:
- Download the 2 root certificates of the domain obr.mos.ru at the links:
- http://caroot.obr.mos.ru/pki/obr.mos.ru_RCA.crt
- http://caroot.obr.mos.ru/pki/obr.mos.ru_RCA(1).crt
- Open the downloaded certificate by right-clicking on the file.
- Install the root certificate in the Trusted Root Certification Authorities container (Figure 5).
Figure 5. Connecting to a closed Wi-Fi network (Windows 8 and earlier)
Aircrack
Aircrack has been around for years, since the days when only WEP (Wired Equivalent Privacy) was responsible for Wi-Fi security. WEP is a weak security, so in 2004 it was replaced by WPA (Wi-Fi Protected Access).
Aircrack-ng is described as a toolkit for accessing Wi-Fi network security mechanisms, so it should be part of every network administrator's arsenal. This kit is used to crack WEP and WPA-PSK keys. It is free and has extensive documentation.
To hack a network, you need the right Wi-Fi adapter in your computer that supports packet injection. You must know how to use the command line and have a lot of patience. Your Wi-Fi adapter and Aircrack must collect a lot of data to be able to decrypt the network key.
You can use Aircrack with a Kali Linux installation or use it to secure your network. A similar option for personal computers is Airgeddon.
Reaver-wps
Cracking much more complex passwords and WPA/WPA2 passphrases requires more effort. Reaver-wps is one of the tools available for this task. Again, command line skills are required. It can take anywhere from 2 to 10 hours to crack it. The password will only work if the router's signal is strong and WPS (Wi-Fi Protected Setup) protection is enabled.
WPS is a button on the router. You also need to press the button on the device with Wi-Fi, then they will detect each other and automatically establish an encrypted connection. This is the loophole through which Reaver works.
Even if you turn off WPS, sometimes the mechanism is not completely disabled. In any case, you should disable this function if you are afraid of hacking. Or use a router that does not support WPS at all.
Hacking Wi-Fi via WPS is possible with some tools on Android, but only if it has been rooted. Options include the Wifi WPS WPA Tester, Reaver for Android, Kali Nethunter.
How the "jammer" works
Unlike real jammers, which interrupt the radio transmitter signal with their stronger signal, the deauthenticator works at the software level. It implements a denial-of-service attack by sending a deauthentication frame to the router on behalf of the devices connected to the network. Since this frame is not encrypted in any way, the jammer only needs to find out the MAC addresses of the devices by sniffing the network traffic.
Deauthentication is usually part of a complex network attack. It is used to create an "evil twin" of the access point or to intercept the handshake, which then allows the password to be decrypted. However, the jammer can also be useful by itself.
![]()
WARNING
All of the tips discussed above are highly recommended for educational purposes only. Data transmission blocking and the use of the means considered may be prosecuted. Penetration tests require appropriate written confirmation from the customer. Remember that deauthorization data is stored in the router's logs.
Recently, inexpensive and miniature boards supporting the NodeMCU software platform have become very popular. They are built on a module ESP8266, which implements the work with Wi-Fi standard 802.11b/g/n at 2.4 GHz. Now there are two versions of such boards: with a chip CP2102 American company Silicon Labs or Chinese CH340.
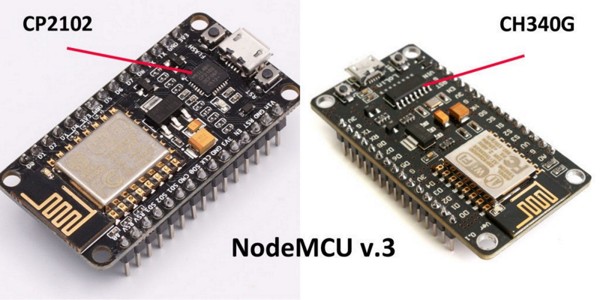
These boards are positioned as devices for prototyping: on their basis craftsmen create automated systems controlled via Wi-Fi. The topic itself is quite fascinating, but we are interested in something else now – the possibility to use the NodeMCU for attacks.
For full monitoring and packet injection the ESP8266 is not suitable, due to technical limitations, but it can be used as a deauthenticator – which led to the appearance of the corresponding firmware. Last year a nice person with a nickname Spacehuhn released the first of them, but since then there are other versions with additional features. However, before moving on to the software, let's define the hardware choice.
![]()
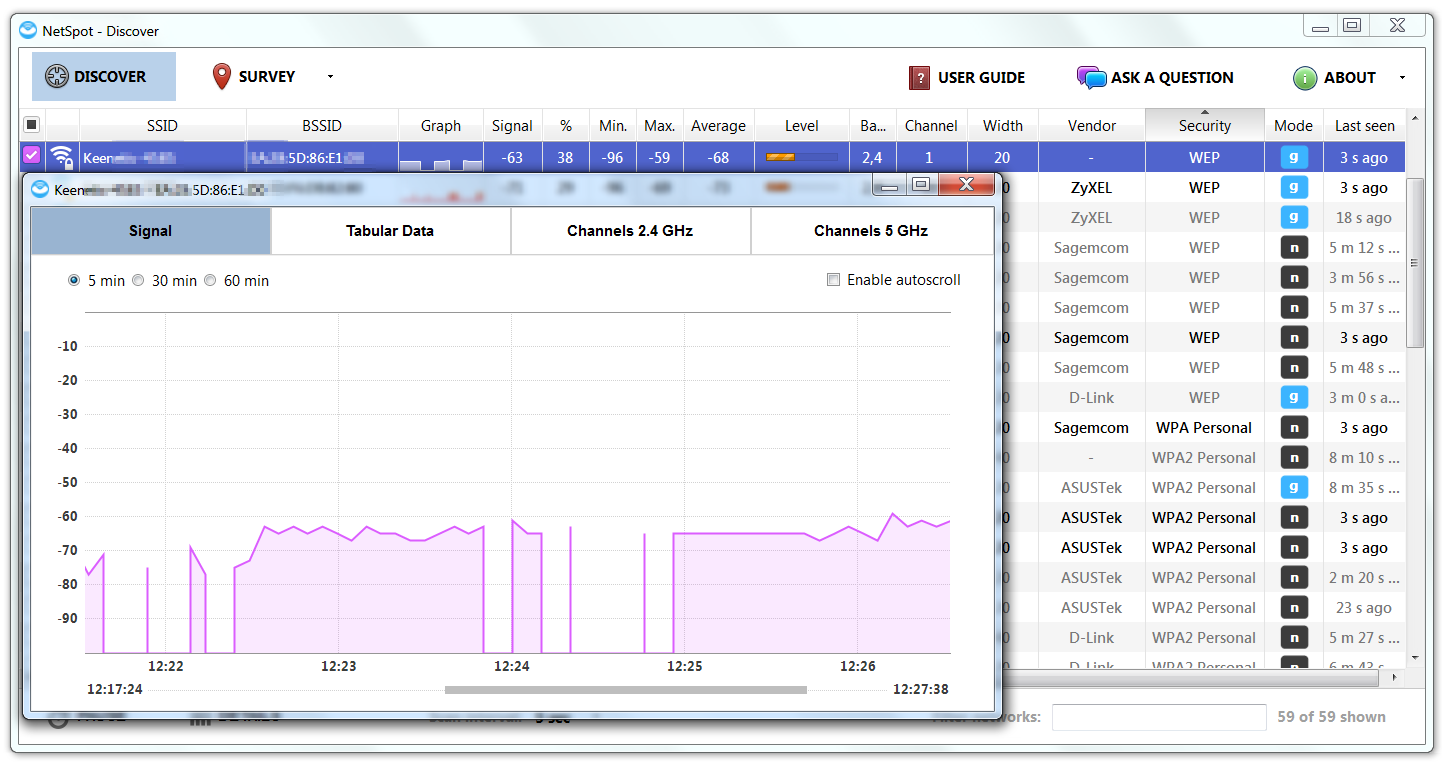
Real time monitoring with NetSpot
If you need to improve the connection in one particular place, you don't have to make a map of the whole room. For that NetSpot has real-time monitoring. In just a few seconds after launch you can get an idea of the overall picture in the air, and then study it more accurately.
You can group the found access points by any parameter, determine their physical location and type of protection, assess the current signal levels in a particular location and their change over time. The latter is especially useful for finding stable access points.
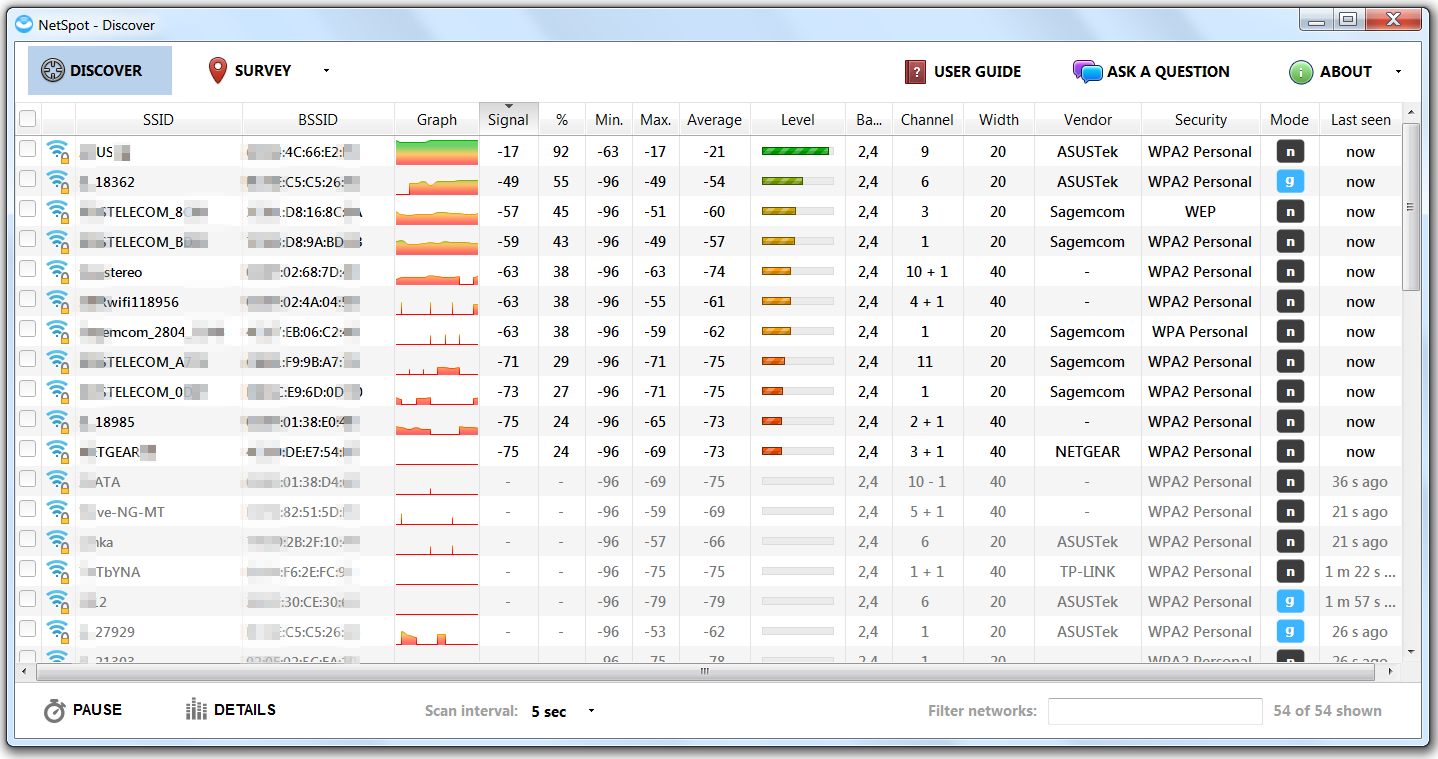
Within a couple of minutes of scanning I found 54 hotspots in the 2.4 GHz band, but a stable connection is only possible with three of them. Another eight APs were more or less catchable, and the connection to the others was only possible with a directional antenna or a powerful amplifier. My main AP is not in the table. The thing is that NetSpot doesn't show the networks with a hidden SSID. I cannot add them manually either.
Looking for APs with weak protection and determining the direction to them
If you connect in Discover mode, it's easy to find potential targets for an attack. Click on the Security tab and you will see a list of hotspots sorted by authentication protocol. Among them, there is one open and twelve consider it open (WEP). Half of them, however, work with slow 802.11g. At the same time, all poorly protected points have a very weak signal. You can only get them with a powerful adapter made by Alfa Networks or a directional antenna, but is the game worth the trouble?
Let's choose one of the WEP-authenticated points and try to reach it with a narrow beam. To do this we take the directional antenna and slowly rotate it. In NetSpot we will mark the desired access point in Discover mode and press Details. As you rotate the antenna the signal from the selected point will sometimes become stronger, sometimes it weakens again. Sometimes it disappears at all. After several minutes of scanning, the direction to it (or to what reflects the signal) is determined. If you use a properly oriented directional antenna, the signal strength will increase. In my case, it went from a miserable -96 dBm to an acceptable -59 dBm.
In general, NetSpot is enough to analyze the signal quality of Wi-Fi of different access points. The fact that you can play "fox hunt" to find out where the unknown hotspots are is a nice bonus.
Exterior Examination
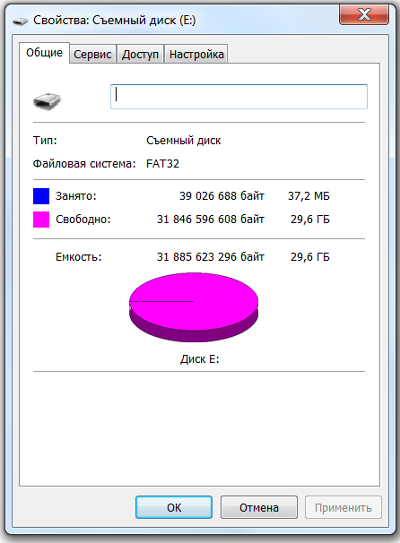
The SanDisk Connect flash drive with wireless module comes in capacities from 16GB to 256GB. For our tests, we bought the 32-gigabyte model. The larger versions are not formatted to FAT32 but to the proprietary exFAT system. Not all the devices support it. A change in the logical partitioning would have affected the tests. The youngest model could have been cut down in something else, so we decided not to take any chances.
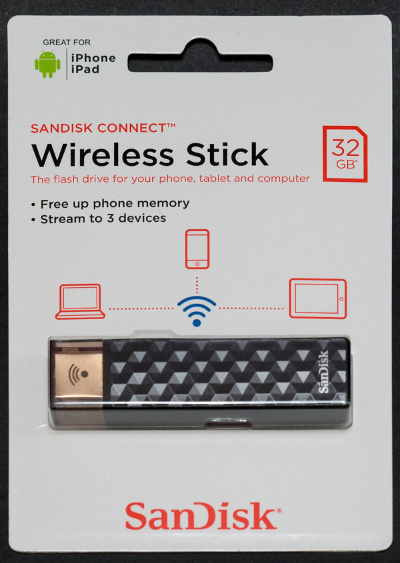
There is 29,6 Gbytes available to the user, 0,04 Gbytes of which is the content recorded by the manufacturer. These are examples of photos, music files and one video clip.
News from the morgue
We opened the flash drive with a real scalpel and at the same time we checked its quality of the construction and maintainability.
It is a typical plastic case consisting of two halves fixed with inner latches. To unbend them you have to move the plastic frame around the connector. Insert the scalpel into the gap close to the opened corner and gently tilt it, pushing the housing parts apart. In the resulting hole insert a piece of thin plastic (such as cut from an old bank card) and move the scalpel a little further around the perimeter. Repeat until the last latch gives up.
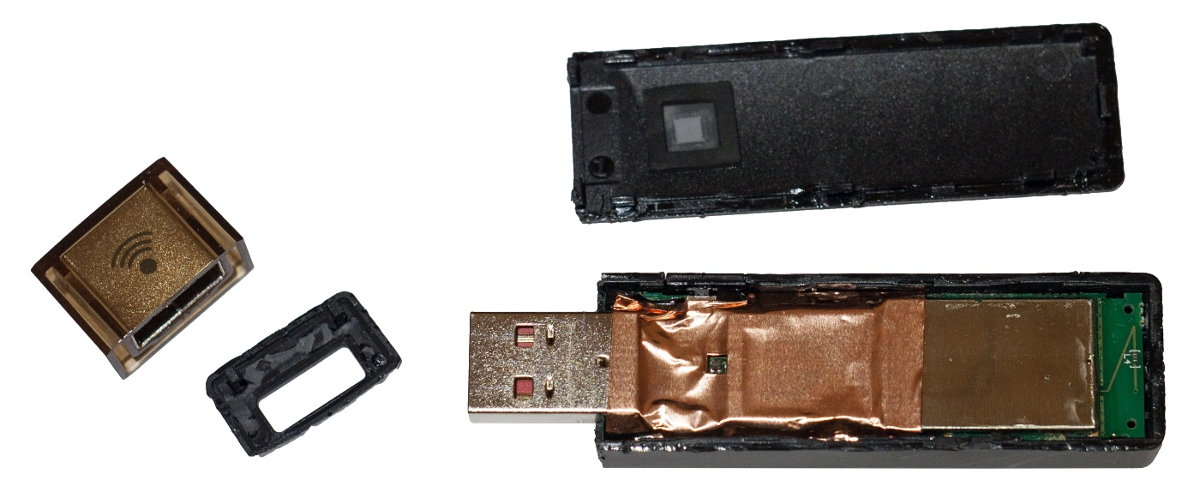
Immediately after opening, nothing interesting can be seen. Everything is covered with foil, which acts as a screen and a radiator. There is a hole only for the LED indicator, and near the connector we can see the foot of the power button.
But on the back side of the board the built-in battery catches the eye. Who complained that its capacity is unknown, and the manufacturer does not report it? The secret is out: 380 mA – h at an operating voltage of 3.7 V gives a capacity of 1.4 W – h with a tail. That's what it says on the battery manufactured by Hangzhou Future Power Technology. The dimensions of the battery are 52 × 16 mm. It will be easy to pick up a replacement based on these parameters.
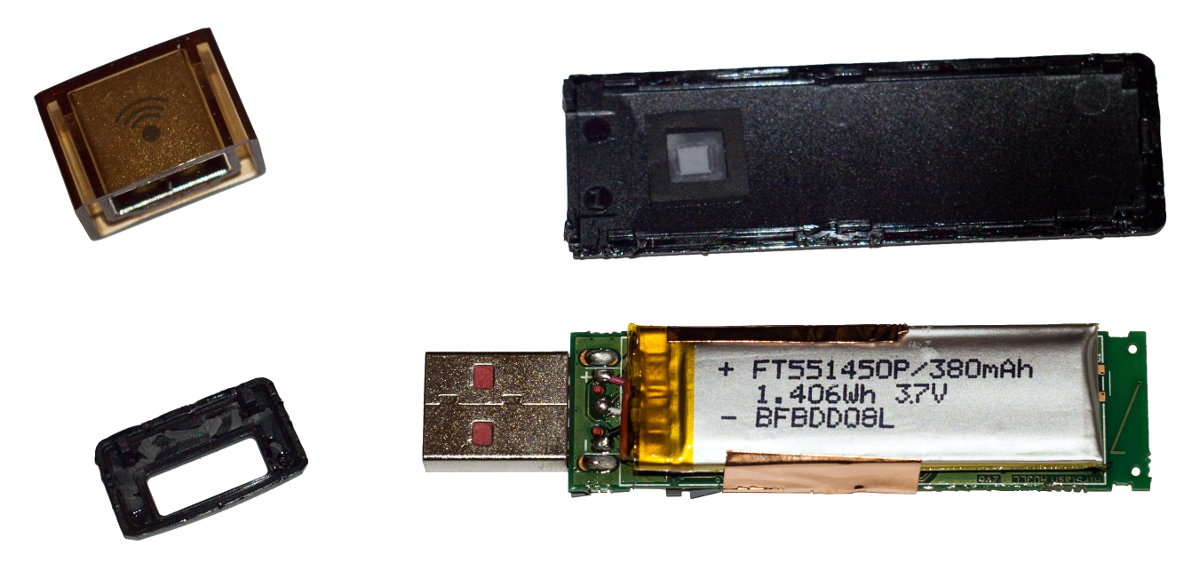
The battery itself is held in place by a strip of double-sided adhesive tape. The back side of the board is visible underneath, and the charge control circuitry can be seen through the translucent film.

On the front side of the board, the foil is glued very firmly. There is a chance of tearing it, so you have to be extra careful at this point. Peel off the foil and… the flash drive turns into a card reader with a slight movement!
Read More: