ExampleLet's imagine that a company needs to install a firewall on an employee's computer. The employee works with personal data of security level 3 – that means she needs a firewall of security level 6 and type "B", to be installed on a network node. This is a screen with the profile IT.ME. B6.PZ. So, you need to look for a firewall with a certificate that matches the selected profile. Higher-level profiles will also work – for example, you could put an IT.ME. B4.PZ.
- How to activate and configure your router's firewall
- Why do I need a firewall on my router?
- What is a firewall
- What are firewalls according to FSTEC documentation
- Firewall
- Firewall protection mechanisms
- Firewall
- IP Reputation
- SSL Inspection
- A firewall is equipment that protects your network
- How does the firewall work?
- Switch, router & firewall: how are they connected?
- What is a gateway?
- What is a network firewall?
- Connection Tracking
- Configuration tips
- Update firmware
- Switch to the 5 GHz band
- What is an SPI firewall?
- What is NAT?
- How does the SPI firewall work?
- SPI vs DPI
How to activate and configure your router's firewall
Nowadays, all operating systems have the firewall preinstalled, but in many cases it is not activated or not properly configured. Routers, which are the brains of the whole network, also have a pre-installed and activated firewall, mostly based on iptables, since the vast majority of firmware is based on Linux. Today in this article we will show you what configuration parameters we can find in the firewall for routers using ASUS routers as well as AVM FRITZ! Box from two manufacturers whose firmware is really complete and gives us great configuration possibilities.
A very important aspect that we must take into account is that when we have the router firewall activated, it is highly recommended to have a firewall on the PC as well, although it is not absolutely necessary, because we are in a NAT environment, so from the Internet They can access our hardware without first opening a port for our PC, or directly opening a DMZ for our PC. In the latter case, it is highly recommended that you install and configure a firewall on your PC, as it will be fully accessible from the Internet.
Why do I need a firewall on my router?
With firewalls, we will be able to allow or block incoming and outgoing traffic through the various interfaces of the router, both on the WAN and the local network. However, the vast majority of users want a firewall on the WAN to control traffic from outside the router itself.
The firewall in the router, will allow us to block any attempt to access a certain port on the router, that is, if we have TCP port 22 SSH open, we can limit the number of simultaneous connections, the number of connections at a certain time, and we can even allow only a certain IP address to access the SSH server of our router.
A very important aspect of router firewalls is that, by default, all connections that start over the border (on the Internet) are denied (DROP) unless they have been specifically allowed before, so a "deny all" policy is the most recommended.
What is a firewall
A firewall (DOE, firewall, firewall) is a tool that filters incoming and outgoing network traffic. It analyzes the traffic source, time of transmission, IP address, protocol, message frequency, and other parameters, and then decides whether to allow or block the traffic.
Firewalls can have default settings – for example, it can block all incoming connections or outgoing packets from certain applications. For corporate purposes, firewalls are usually configured additionally – specifying protocols, ports, and application permissions. This is usually handled by a system administrator or an information security specialist.
A classic firewall does not inspect transmitted data, does not look for malicious code, and does not encrypt or decrypt anything. It works only with the network parameters of a connection, to be more precise, with the features of the particular IP packets that make up that connection, such as the IP addresses of the connecting computers and some other parameters.
The firewall acts as a barrier between two networks, such as a company's internal network and the Internet. It protects against:
- Unauthorized access from the Internet to the protected network. For example, if a data packet arrives from the Internet from an untrusted recipient, the DOE will not let it through.
- Unmonitored network connections. If someone tries to launch a DDoS attack to bring down the company's servers, the DOE will not let those data packets through.
- Unauthorized transmissions from the protected network to the Internet. For example, a virus has infiltrated a server, collected data, and is trying to send it to a hacker. The DOE will notice the transmission to a suspicious recipient and block it – the data will not leak into the network.
Most often a firewall is installed on the perimeter of a corporate network and the Internet. But you can also install it inside the corporate network to create a separate, particularly protected network. For example, you can additionally filter the traffic to the servers with the most secret data. Besides, the shield can stand on a separate computer and protect it only. In this case, it is sometimes called a network firewall (not a firewall), but it will also be classified as a firewall by the FSTEC.
What are firewalls according to FSTEC documentation
Firewalls are of two types: hardware and software. They perform the same functions but work in slightly different ways:
- Hardware-software complexes (HSCs), or hardware DOEs – Special devices or router components that have filtering software installed. All hardware and software inside this device is specialized for traffic filtering and several related tasks, additional programs cannot be put on a hardware DOE. This reduces the vulnerability of such a device to attacks and allows for higher class protection.
- Software DOE – Software on the server that filters the traffic. This is essentially the same software that is installed in a hardware DOE, but it is installed on the server itself.
Hardware DOEs are usually at the edge of the network, for example where the intranet connects to the Internet. Software DOEs are at the nodes of the internal network itself, that is, they protect the computers and servers themselves.
Hardware DOEs are more expensive, but more reliable and provide more serious protection. Software firewalls are cheaper, but less reliable – there is a risk that traffic from an intruder will manage to damage the network. In addition, software firewalls often put so much strain on the computer they are installed on that nothing else can be installed there. Because of this, they sometimes have a separate server dedicated to them – and this server actually plays the role of a hardware firewall.
A firewall can also be deployed on a cloud server. It can be placed on the edge of a logical LAN in the cloud, just as a physical DOE can be placed on the edge of a physical corporate network. This DOE will filter connections at the edge of the virtual private network.
Firewall
The usual suite of built-in ITU (firewall) features – antivirus, IDP, application patrol – allows you to inspect traffic up to OSI layer 7. In addition, there are other control features not found in conventional routers.
Of course, many firewalls have the standard "gentleman's kit" of a typical router. But the "strength" of the ITU is determined by the availability of filtering and traffic management functions, as well as by the enhanced hardware to implement these tasks.
It is worth noting that the set of filtering capabilities of a particular ITU device does not mean at all: "The more features we were able to 'tweak', the 'better' the firewall". The main mistake would be to focus on the length of the list of all sorts of "features" when buying, without taking into account the specific purpose, design features, performance parameters and other factors. Everything must be strictly dosed and balanced without any bias towards "super security" or "super economy".
And here the network administrator faces his first problem. While for the SOHO segment it is not too difficult to formulate a typical set of requirements, for the corporate segment it requires additional preparation. To better meet the needs of the business, there are different devices – each for its own niche. For example, for a VPN Gateway, the security feature set certainly plays a big role, but the primary goal is still the creation and maintenance of working VPN channels. An example of such a device is the ZyWALL VPN1000

But for Secure Gateway, all sorts of filters, "Sandbox" and other types of checks are in the first place. The ZyWALL ATP800 is an example of such a specialized device for increasing the level of security.

Firewall protection mechanisms
Now that we've discussed the differences between routers and firewalls, and between different types of firewalls, it's time to talk about methods of maintaining the required level of security. What are some of the layers of protection that traffic goes through that help keep your network secure?
Firewall
This service is inherited from routers. The firewall monitors and blocks unwanted addresses, closes ports, and analyzes other characteristics of packets that can be used to "figure out" unwanted traffic. At this stage there is a reflection of a large number of threats, such as attempts to connect to public TCP ports, packet bombardment in order to disable the system and so on.
IP Reputation
This is a cloud-based extension of the regular firewall features and is a definite step forward. The point is that normally the system knows nothing about the source or the destination (depending on the type of traffic). If this is not explicitly spelled out in the firewall rules, such as "Deny", then traffic will pass through, even from the most malicious sites. The IP Reputation function allows you to check if an IP address is suspicious or "flagged" in a reputation database. If the database says that the IP address has a bad reputation, we can leave the traffic unchanged, disallow it entirely, or allow it under certain conditions.
The checking is quick because only the IP address and a short query are sent, the answer also comes in a very brief form which does not affect the traffic volume very much.
SSL Inspection
Allows you to inspect SSL-encrypted traffic, so that the other ITU profiles can expose packets and handle SSL traffic as unencrypted. When the information flow is protected from external access by encryption, it is not possible to verify it – this also requires access to its content. Therefore, during the inspection phase, the traffic is decrypted, read by the control system and re-encrypted, and then transmitted to the destination.
A firewall is equipment that protects your network
A firewall (ITU) is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or deny specific traffic based on a set of established security rules. Firewalls are used as the first line of defense for networks. They put a barrier between secure, controlled internal networks that can be trusted and untrusted external networks such as the Internet.

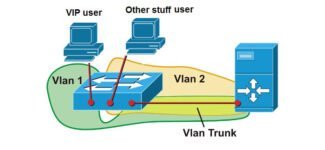
Figure 5: Firewalls establish a barrier between the Internet and the intranet/local network.
In addition to separating the LAN from the Internet, firewalls can also be used to segment important data from ordinary data on the LAN. This can also avoid internal intrusion.

Figure 6: A firewall segregates important data from other data.
How does the firewall work?
One common type of firewall hardware allows you to define blocking rules, such as IP address, Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) port. Therefore, unwanted ports and IP addresses are denied. Some other firewalls are software applications and services. These firewalls are like a proxy server that connects two networks. The internal network does not communicate directly with the external network. A combination of the two is usually safer and more efficient.
Switch, router & firewall: how are they connected?
Usually the router is the first thing you will have on your LAN, the firewall between the internal network and the router allows you to filter all incoming and outgoing flows. Then comes the switch. Since many ISPs now provide Fiber Optic Service (FiOS), you need a modem in front of the firewall to convert digital signals into electrical signals that can be transmitted over Ethernet cables. Thus, a typical configuration would be an Internet modem-modem firewall-switch. The switch then connects other network devices.

Figure 7: How a switch, router, and firewall are connected in a network.
What is a gateway?
A gateway is a network hardware device or network node designed to connect two different networks together, allowing users to exchange data across multiple networks. The most common gateways are computers and routers that connect the enterprise to the network. They are needed to communicate between terminals connected to heterogeneous networks with different network characteristics and using different protocols.

What is a network firewall?
A firewall is designed to monitor incoming and outgoing network traffic and decide whether to allow or block certain traffic based on a set of security rules. It can put a barrier between your internal network and incoming traffic from external sources (such as the Internet) to block malicious traffic such as viruses and hackers.
A firewall can be either software or hardware (it is best to have both on your network). A software firewall is a program installed on each computer that regulates traffic through port numbers and applications, while a physical firewall is a piece of hardware installed between your network and the gateway.

Connection Tracking
Another important thing to understand about firewalls is the Connection Tracking (or simply ConnTrack) mechanism. RouterOS has a special table which stores information about connection states. This is how NAT and many other parts of the firewall work.
ConnTrack mechanisms check if a packet arriving at a router belongs to any of the streams, so that they can apply policies to the entire stream or somehow arrange packets within one or more streams (for example, to slice rates).
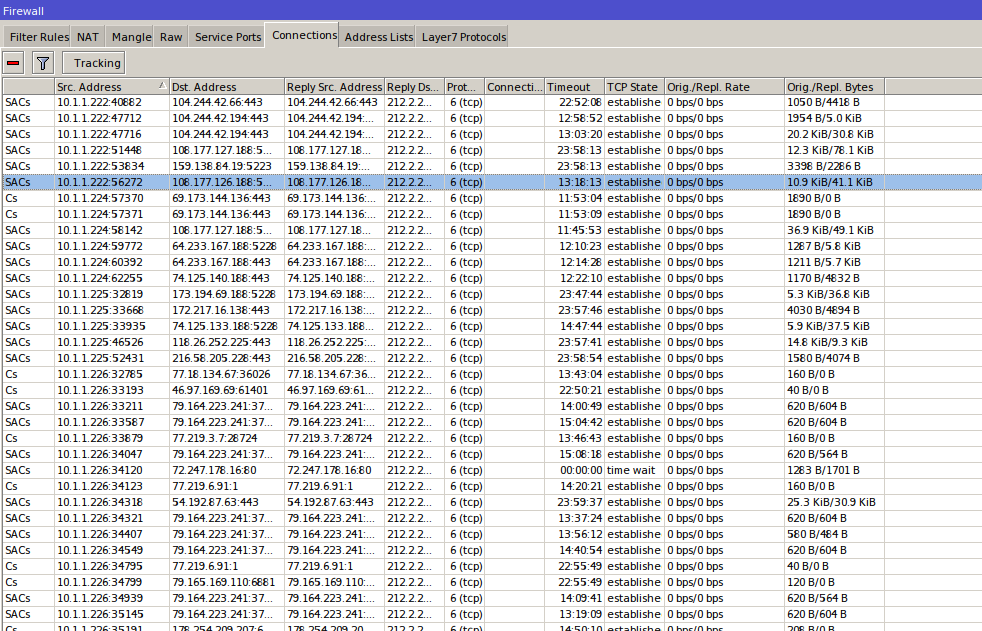
- new – a new packet that does not belong to any of the known threads. This could be the first packet to connect to an RDP server, or the first packet in a WinBox thread, or a DNS query. The system remembers the Source IP, Source Port, Destination IP, Destination Port and some other parameters and writes this data to a table. Next packet with the same data will refer to the written stream;
- established – the packet belonging to an existing flow. That is, a packet with a Source IP, Source Port, Destination IP, Destination Port that matches one of the entries in the ConnTrack table (or a reverse packet);
- related – A packet originating from a different flow. Some protocols such as FTP, SIP, PPTP use multiple flows to work. For example, FTP control commands go on TCP port 21, but data is transmitted from TCP port 20. When you try to fetch or send data to FTP in a thread on port 21, the server says, "Now I will open port 20, and you fetch data from it," then the client sends a packet to port 20 of the server. This packet will be considered related because it is generated by the port 21 stream;
- invalid – all that is not related to the above states. Example: The session closed correctly, but due to routing errors, some packets from the middle of the session flew out the other way. When they arrived, their session is already closed and the router knows nothing about them. They are not new and do not belong to existing connections, so we consider them invalid.
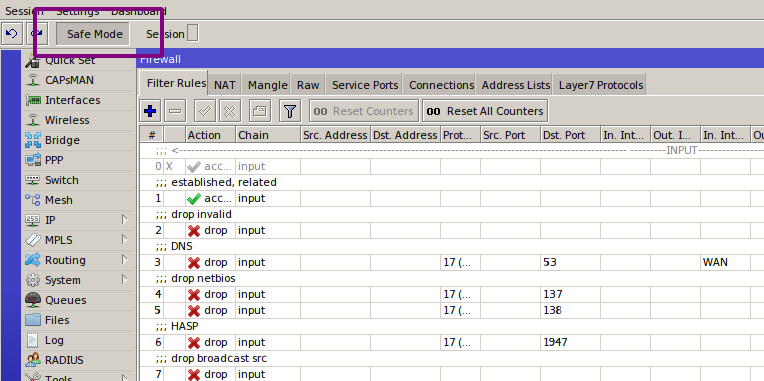
Configuration tips
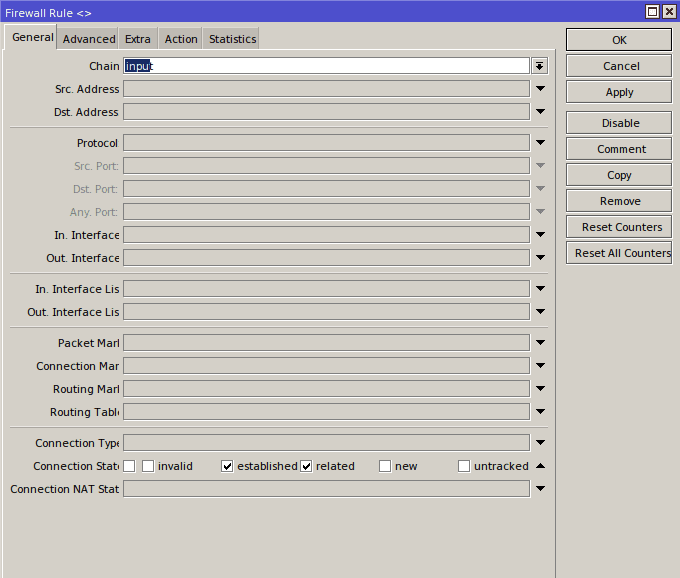
Let's move on to the practice of setting up. In this article I will talk about the Filter table, the one which filters the traffic. As we found out a little bit above, the input chain is responsible for the traffic to the router itself, and the forward chain is responsible for the traffic that goes through the router. Now let's start protecting the router itself.
The first and most important thing to remember when working with a firewall was described back in the lost chapter of The Tale of Igor's Campaign: "remote configuration of the firewall is for the long haul". So respect your ancestors and use Safe Mode.
The way this mode works is that you press the Safe Mode button in the interface, and it stays pressed. From there you do whatever you were going to do, but the changes will only apply when you click the button again. If they cause the router and WinBox configurator to stop communicating (for example, if you have filtered your own packets or disabled the interface), the router will return to the state it had before you entered Safe Mode.
Only 100 actions are memorized, but that's enough for most cases. There will be no reboot – the rollback is instantaneous. From the console, this mode is activated by Ctrl-X.
Neither of them can be called unequivocally correct. I am a follower of the second approach, but in unfamiliar networks, I use the first.
In order to allow the desired traffic, you need to define this traffic. In the case of input, this is quite easy. Here is what you need for the router to work properly.
- Management: WinBox, SSH, in some cases WebFig, for example to view load graphs.
- If the ISP gives an address via DHCP, then enable this protocol on the external interface.
- If the router is a DHCP server, enable it on the internal interfaces.
- This is the same for DNS.
- If you want to bring up tunnels, enable them.
- OSPF.
- ICMP.
- NTP.
- Neighbor Discovery.
- SNMP.
- Other services.
Update firmware
Every self-respecting router manufacturer is constantly improving the software of its equipment and regularly releases updated versions of the firmware ("firmware"). In the latest versions, first of all, detected vulnerabilities are fixed, as well as errors that affect the stability of operation.
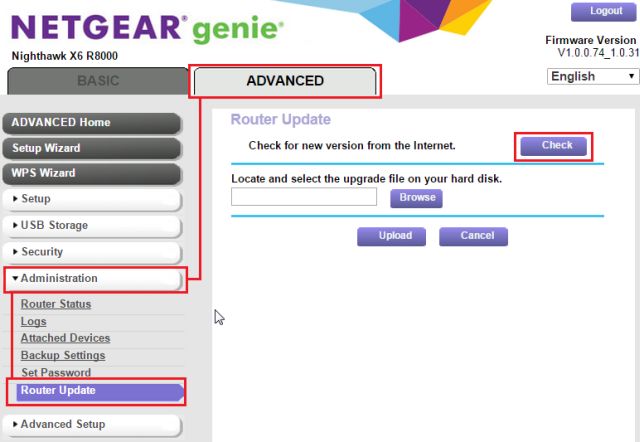
That's why we strongly recommend that you regularly check for firmware updates and install them on your router. In most cases this can be done directly through the web interface.
Please note that all the settings you have made may be reset to factory defaults after the update, so it makes sense to back them up – also via the web interface.
Switch to the 5 GHz band
The basic Wi-Fi range is 2.4 GHz. It provides reliable reception by most existing devices up to about 60 meters indoors and up to 400 meters outdoors. Switching to the 5 GHz band will reduce the communication range by two or three times, limiting the possibility for intruders to penetrate your wireless network. With less band occupancy, you'll also notice an increase in data transfer speed and connection stability.
The only disadvantage of this solution is that not all devices work with IEEE 802.11ac Wi-Fi in the 5 GHz band.
What is an SPI firewall?
SPI stands for Stateful Packet Inspection. It is an advanced firewall for network security.
Stateful Packet Inspection firewalls or packet filtering only check the source and destination IP address as well as the source/target port and allow incoming traffic to communicate with the right device on the network. We explained in our previous blogs how to move forward and why it may be necessary for certain activities (such as gaming) for a better experience. The stateful firewall is more complete in comparison. But first, let's understand how NAT works.
What is NAT?
Network address translation is the part of your router that keeps track of all outgoing requests in the NAT table. It notes the IP address of each device, which port it used, and the IP address and destination port it wants to connect to over the Internet.
It then maps your device to a single IP address, also called a gateway, assigned by your Internet Service Provider (ISP). Since there is a finite number of IP addresses that we are nearly exhausted, this approach gives us the time we need before IPv4 addresses are exhausted. You can learn more about IPv4 addresses here.
A NAT firewall is a stateful firewall that only follows certain rules to allow/deny entry for data packets.
How does the SPI firewall work?
Network traffic moves in small chunks called data packets. Your communication with a friend over the Internet is based on a series of data packets. Each data packet carries some information that is transmitted and then created at the destination.
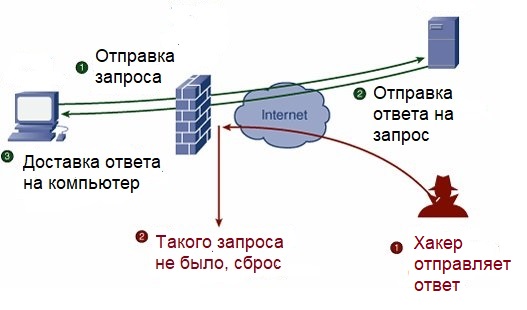
Instead of just tracking the source and destination addresses, the SPI firewall checks the context of the data packets. It checks certain things, such as whether the data packet belongs to the active session established after the TCP handshake. It works with both TCP and UDP. In the case of UDP, which transmits data packets without receiving confirmation, it follows the configuration (allowed session duration, for example).
The SPI firewall has its own memory, which it uses to record previous data packets and uses a state table to determine if the next packet is part of a series. It knows which application has requested an Internet connection and expects to hear back from the web server. The SPI firewall discards the data packet if certain conditions are not met.
For example, when you request to open a website, the SPI firewall will write the request to its memory. This way, the incoming response will be trusted because it knows the internal application requested for it. SPI is useful because it can open/close ports, allowing traffic to pass through NAT, which the firewall cannot do without preserving state.
This is useful for basic security, where the firewall will discard data packets containing malware rather than part of a series sent by an attacker.
This kind of security process results in a loss of performance.
SPI vs DPI
Deep packet inspection (DPI) is now a more advanced firewall. It works at a deeper layer of the OSI model than the SPI firewall. Where SPI inspects data packets by checking things like the packet header, source, active connection, etc., DPI breaks up the data packet. We're talking about actually checking the payload to make sure it complies with the rules.
Read More: