This approach has one big disadvantage – since the password (or login-password, which is essentially just two parts of the same password) is transmitted over the channel "as is" – anyone can get in between you and the client and get your password on a platter. And then use it and dispose of you however they want!
WPA vs. WPA2: which WiFi security protocol should you use?
Wireless networks are everywhere. If you're in a coffee shop, school, or home, there are likely several wireless networks you can access. But how do you know which ones are safe? Check their security settings-they can be a good indicator of which of these networks you can trust. To help you with this question, we'll discuss the history of the WPA and WPA2 security protocols and compare them to each other.
When you install Wi-Fi, you have several options for router security. If your router is left unprotected, unauthorized people can access it, use it for illegal activities on your behalf, monitor your Internet usage, or even install malicious software.
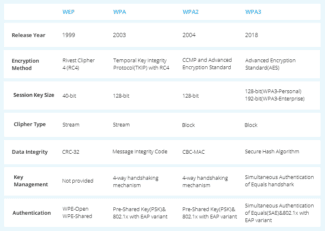
When you set up wireless security, you will have several options available to you: for example, none, WEP, WPA, WPA2-Personal, WPA2-Enterprise, and possibly WPA3. Depending on how you plan to use the Internet, you may need more or less security.
History of security protocols
Wireless security has changed over time to become more secure, but also easier to set up. Since the advent of Wi-Fi, we have gone from WEP to WPA3. Let's look back at the history of these security protocols.
Wired Equivalent Privacy (WEP)
The first security protocol was called Wired Equivalent Privacy or WEP. This protocol remained the security standard from 1999 to 2004. Although this version of the protocol was designed to be secure, it nevertheless had a rather mediocre level of security and was difficult to configure.
At the time there was limited importation of cryptographic technology which meant that many vendors could only use 64 bit encryption. This is a very low bit encryption compared to the 128-bit or 256-bit options available today. Eventually, the WEP protocol was not developed further.
Systems that still use WEP are not secure. If you have a system with WEP, it should be upgraded or replaced. When connecting to Wi-Fi, if the institution uses WEP, your Internet activity will not be secure.
WiFi Protected Access (WPA)
The Wi-Fi Protected Access or WPA protocol was created in 2003 to improve the functionality of WEP. This improved protocol still had relatively low security, but was easier to configure. WPA, unlike WEP, uses the Temporary Key Integrity Protocol (TKIP) for more secure encryption.
Since the Wi-Fi Alliance made the switch from WEP to the more advanced WPA protocol, they had to keep some elements of WEP so that older devices would still be compatible. Unfortunately, this means that vulnerabilities such as the WiFi Protected configuration feature, which can be hacked relatively easily, are still present in the updated version of WPA.
Features
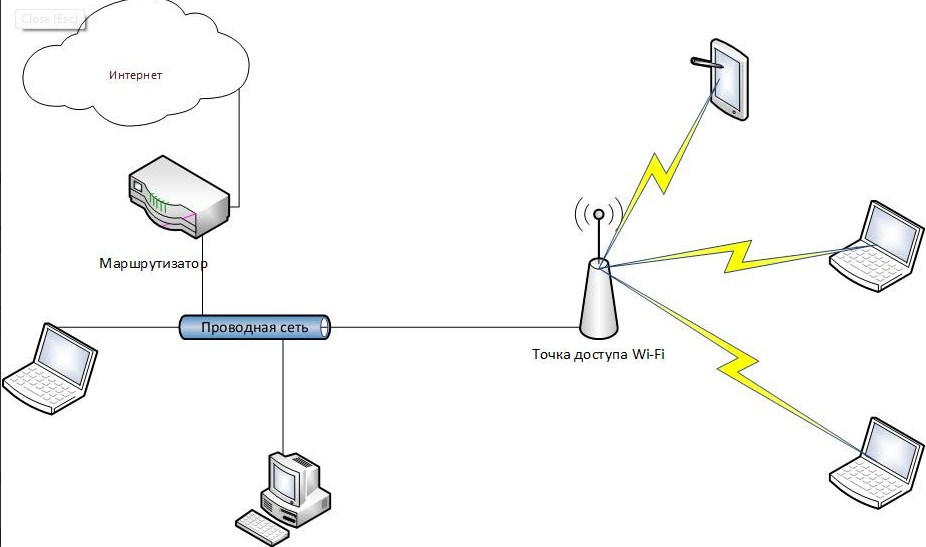
What is Access Point (AP) Mode? We will talk about features in the context of a comparison with the router mode.

- Let's take a situation like this. At home there is a wired network, computers, printer, TV set-top box are connected to the router but all the LAN ports are busy. And we need to connect another smartphone and laptop, and they are standing in another room where the signal of the existing network is bad. We turn on the additional router access point mode, connect both devices and the problem is solved – without unnecessary wires all home devices are connected to the same network and get access to the Internet.
- In order to connect to the Internet, you may need to configure the connection settings. For Access Point Mode, you will have to make them on each device. In Router Mode, you set up once – you create a wireless network and then you can connect to it.
- A router, as opposed to an access point, has network protection against attacks and the ability to limit traffic. Of course, you have to make the appropriate settings, but it is worth it – you get protection against network attacks, you can determine the speed for certain devices and enable traffic prioritization.
- Router mode has more options, but that means it's more complicated to set up. You can name your wireless network and make up a password for it. You can do port forwarding, enable parental control, many devices have the ability to create a guest network, and more.
- The access point as an independent device doesn't distribute IP, doesn't connect to the ISP – it just gets the Internet from the router and distributes it further "over the air". However, some can do it all, but there are nuances, and the cost of such access points will be comparable with the price of routers. Therefore, in this situation, it is better to buy a full-fledged router.
How to enable AP Mode on the router?
So, we have a primary and a secondary router which will work as an access point. To make it work, you need to enable Access Point mode and connect both devices with a network cable (via LAN ports). How to do this on different models, I will now tell you.

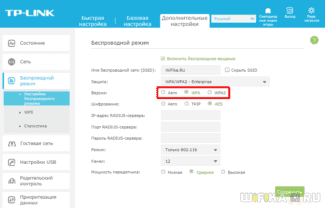
TP-Link
Instructions will be based on the example of N-series router models:
- Go to the admin panel of the device you want to configure as an access point, open any browser, type the IP address in the address bar (possible variants – 192.168.1.1, 192.168.0.1, tplinkwifi.net or tplinklogin.net) and log in (default login/password – admin/admin).
- We need to change the IP address: on the left side, look for the "Network" section and go to "LAN".
- In line "IP address" we write the same as for the main router, but change the last digit, click "Save.
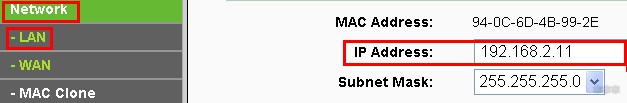
- Do reboot and go to the admin panel, using the newly set address.
- Set up the Wi-Fi connection in the section "Wireless mode" – come up with a network name and security key.
- Go to the section "DHCP", go to the settings and disable the DHCP server, save the changes.

ASUS
- Go to the admin panel – IP 192.168.1.1, login/password – admin/admin.
- In the menu on the left, look for the "Administration" section, then go to the tab "Mode of operation".
- Select the access point mode, press "Save".
Connecting modes of operation
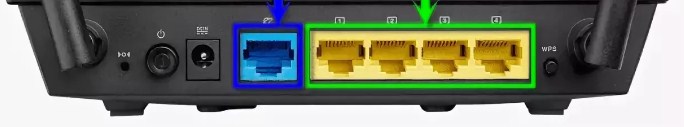
Let's take a look at the router first. It has a blue port for the ISP wire and local ports. Well, there are two antennas on the sides to strengthen the Wi-Fi signal.

But this one is an access point and it has only one port. So the connection will be like this. Sometimes you can see the PoE port. It is designed for powering through the network wire in places where there are no sockets.
NOTE! As mentioned earlier, another router can act as an access point. To do this, simply configure it by going to the Web interface. But on some devices there is a special switch of modes.
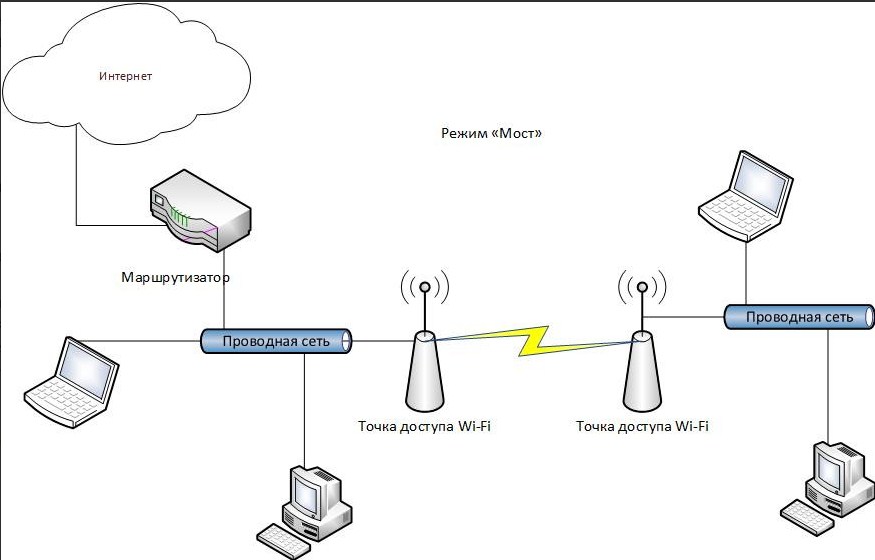
But also the access point can work in "Bridge" mode. In this case, the second device connects to the network of the first one via Wi-Fi. And the wired port is used to connect several devices. For this purpose, an ordinary switch is suitable.
But it is possible not to use a wired port at all, and to receive and send a signal only through the air. In this case the device turns into a wireless access point, working in the "Repeater" mode.
There is one more interesting mode of this device. It is called a WISP receiver. This technology is widely used in rural areas, where there are special WISP stations, which distribute Wi-Fi with the Internet for several kilometers.
Varieties of
- External – Are installed outdoors. They have a more robust housing, as well as protection from moisture, dust and cold. Before buying, be sure to look at the allowed temperature mode, which will depend on the winter of your region.
- Indoor – are installed at home and have no special protection.
It is also possible to divide by the form and method of connection to the network:


Wi-Fi security mechanisms
Technologies are man-made and almost all of them have bugs, sometimes critical enough to bypass any theoretically good protection. Below we'll run through a list of existing security mechanisms for transmitting data over the air (that is, without mentioning SSL, VPN, and other higher-level methods).
OPEN

OPEN – is the absence of any protection. The access point and the client do not mask the data transmission in any way. Almost any wireless adapter in any Linux laptop can be set in sniffer mode, where instead of discarding packets not destined for it, it will capture them and transmit them to the OS, where they can be safely viewed. Who's on Twitter there?
This is exactly how wired networks work – they have no built-in protection and if you "break into" it or just connect to a hub / switch network adapter will receive packets of all devices in this segment of the network in the open form. However, with a wireless network you can "break into" from any place – 10-20-50 meters or more, and the distance depends not only on the power of your transmitter, but also on the length of the hacker antenna. Therefore, open data transmission over a wireless network is much more dangerous.
This article series will not discuss this type of network, since there is nothing to hack. If you need to use an open network in a cafe or airport – use VPN (avoiding PPTP) and SSL ( https:// , but put HTTPS Everywhere, or be paranoid about the lock suddenly disappearing from the address bar if someone turns on sslstrip – which, however, will not save the passed passwords), or even all together. Then no one will see your cats.
WEP

WEP – is the first standard for Wi-Fi security. It stands for Wired Equivalent Privacy ("Wired Equivalent Privacy"), but in fact it gives much less protection than those same wired networks, as it has many flaws and is hacked in many different ways, which because of the distance covered by the transmitter makes data more vulnerable. It should be avoided almost as much as open networks – it provides security only for a short time, after which any transmission can be completely exposed regardless of the complexity of the password. The situation is exacerbated by the fact that passwords in WEP are either 40 or 104 bits, which is an extremely short combination and can be cracked in seconds (that's not taking into account errors in the encryption itself).
Easy Connect
Easy Connect is an acknowledgement of the vast number of devices connected to the network in the world. And while not all people may want to get smart homes, the average person probably has more devices connected to their home router today than they did in 2004. Easy Connect is the Wi-Fi Alliance's attempt to make connecting all these devices more intuitive.
Instead of having to enter a password every time a device is added, the devices will have unique QR codes – and each device code will work as a public key. To add a device, it will be possible to scan the code with a smartphone already connected to the network.
Once scanned, the device will exchange authentication keys with the network to establish a follow-up connection. The Easy Connect protocol is not WPA3 related – devices certified for it must have a certificate for WPA2, but not necessarily a certificate for WPA3.
Enhanced Open
Enhanced Open is another separate protocol designed to protect the user on an open network. Open networks-such as the ones you use in a coffee shop or an airport-carry a whole host of problems that don't usually concern you when you're establishing a connection at home or at work.
Many of the attacks that occur on an open network are passive. When a bunch of people connect to a network, an attacker can collect a lot of data just by filtering the information that passes by.
Enhanced Open uses Opportunistic Wireless Encryption (OWE), defined in Internet Engineering Task Force RFC 8110, to protect against passive eavesdropping. OWE does not require additional security with authentication – it focuses on improving the encryption of data transmitted over public networks to prevent its theft. It also prevents so called. unsophisticated packet injection, in which an attacker tries to disrupt network operation by creating and transmitting special data packets that look like part of normal network operation.
Enhanced Open does not offer protection with authentication because of the way that open networks are organized – they are, by definition, meant to be used by everyone. Enhanced Open was designed to better protect open networks against passive attacks, so that it does not require users to enter additional passwords or go through additional steps.
It will be at least a few years before WPA3, Easy Connect and Enhanced Open become the norm. WPA3 will not become widespread until routers are replaced or upgraded. However, if you are concerned about the security of your personal network, you can replace your current router with one that supports WPA3 as soon as manufacturers start selling them, which may be in a few months.
Read More: