Here Lck No means that WPS is not blocked (you can use it). The vulnerable vendors are Ralink, Broadcom and Realtek. For WPS brute-forcing, reaver is the best utility right now. Let's use it:

- Installing, Configuring, and Using Wifite
- Automating WiFi hacking with Wifite
- Installing Wifite
- Using Wifite
- Selecting the attack mode
- Launch an attack
- Conclusion
- Attacking all access points with WiFite
- Wifite or Wifite2?
- WiFi hacking procedure
- Hackers House Nepal
- Popular Posts
- Tutorial Install WiFite On Kali Linux
- WiFite Features
- Required Tools
- Learn Install And Run WiFite On Kali Linux Step By Step
- Хэндшейк
- Theory of a Handshake Hack
- Phishing
- Hacking WEP network
- Troubleshooting
Installing, Configuring, and Using Wifite
In the article "Current WiFi hacking methods", we discussed all working methods of WiFi hacking. In this article, we will continue the topic of Wardraiding (finding and hacking WiFi access points) and get acquainted with the Wifite tool. I will show you how to install and use Wifite.
Often when pentesting, we have multiple Wi-Fi access points to test for security. Instead of testing each one individually with tools like aircrack-ng, Reaver, pyrit, hcxdumptool and others, we can automate this testing with a single tool like Wifite.
Automating WiFi hacking with Wifite
Wifite is a tool for automating Wi-Fi password cracking that uses almost all known WiFi hacking techniques such as Pixie-Dust attack, PIN bruteforcing, NULL PIN attack, WPA handshake + offline hacking, PMKID Hash Capture + offline hacking and various WEP hacking techniques.
Installing Wifite
Wifite is installed by default in Kali Linux. If you use another distribution or you don't have Wifite installed for some reason, then use the following command to install Wifite:
Using Wifite
Like any other tool to crack the wireless password, Wifite must be set in monitor mode. Once launched, the tool does it by itself, but if it doesn't, you can do it manually:
Let's see if Wifite can crack networks with WEP, WPA and WPS.
I always recommend to start with the help:
If you have trouble starting it, try running the toolkit with the — kill directive to stop conflicting processes.
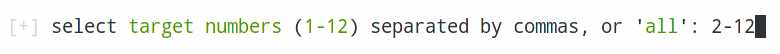
After starting and scanning the air, a list of WiFi networks will appear:

Stop scanning by pressing CTRL + C and select the network. For the hack, I chose my access point "Hack_Me_If_You_Can" with WEP protection enabled.
As soon as you enter the network ID (in my case it is "1") Wifite will start the attack.
Selecting the attack mode
Wifite offers several attack modes for Wi-Fi networkswhich you can choose depending on your needs.
- Dictionary attack (WPA / WPA2) – Uses a dictionary of passwords to try and crack the password Wi-Fi network. It requires you to download a dictionary of passwords that can be found on the Internet, or to create your own.
- WPS attack – Uses vulnerabilities in the WPS (Wi-Fi Protected Setup) protocol to crack the password Wi-Fi network. This method only works on Wi-Fi networks that use WPS.
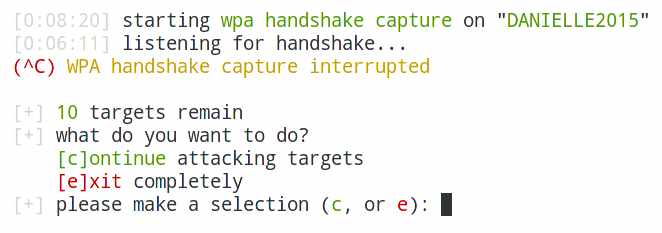
- Handshake attack (WPA / WPA2) – Uses a handshake between the client and the access point Wi-Fi to crack the password Wi-Fi network. This requires grabbing the handshake and using it to crack the password.
Select the desired attack mode by pressing the corresponding key on the keyboard and press Enter ..
Launch an attack
Once you've selected an attack mode Wifite . automatically starts scanning for wireless networks in the surrounding area and displays the list of available networks.
Select the desired network by pressing the corresponding key on the keyboard and press Enter. Wifite launches an attack on the selected Wi-Fi network using the selected attack mode. During the attack Wifite shows information about the attack progress, including the speed and the number of password cracking attempts.
If Wifite has successfully cracked the password Wi-Fi network, it automatically saves the password to a file and continues to attack other networks.
Conclusion
Remember that this article is written for information purposes only, as well as to conduct a security audit of your own Wi-Fi network. Using this knowledge for selfish purposes, or with bad intentions to cause harm, is punishable by law. Attacks on Wi-Fi networks are very common nowadays, that's why it is important to secure them. Bruteforce or other attacks can give an attacker access to your network and who knows what he will do with that access. WiFite tool will help you protect your network from this type of attack and you will be able to protect yourself from hacking and penetrating your Wi-Fi network. You can get more information about WiFite on the GitHub page.
That's all for today. I hope this article will be useful for you.
Cyber-X Magazine
Attacking all access points with WiFite
Although WiFite performs automatic hacking, user intervention is required at least once. – when we need to select access points for the attack. By using the –all key, you can instruct wifite to attack all access points at all, in which case no user action will be needed at all.
WiFite is probably the best program for beginners. You can hack your first wireless access points with it without knowing anything about handshakes, deauthentication, Wi-Fi encryption types, and technologies such as WEP, WPS. Personally, my first successful experience that made me believe in my abilities and awakened my interest in this subject was with the wifite program.
Wifite has no equal in terms of effort / results obtained. Nevertheless, when you develop the pentesting of wireless Wi-Fi networks, working with your hands and head, you can achieve greater results. A pentester with experience only needs a quick glance to see low-potential access points (very weak signal or no clients), if the pentester detects a WPS, it will not get stuck on it for hours, stopping other work (wifite will get stuck, which is basically correct, since WPS is often hackable). Pentester would try to grab every possible handshake and then, while the hashes are going through, launch attacks on WPS and WEP.
It probably depends a lot on conditions, but with proper skill I've had it easier to get handshakes using airodump-ng + aireplay-ng than using wifite.
By the way, to automate handshake capture, we recommend reading the article on using the new zizzania tool: "Mass Automated Handshake Capture in BlackArch using zizzania".
Программа WiFite содержит множество опций, познакомиться с ними вы можете на странице документации в Энциклопедии инструментов для пентестинга.
Wifite or Wifite2?
Wifite is not a new tool. It was one of the first WiFi hacking tools we met. Along with Besside-ng, automated scripts for hacking WiFi allowed even the script kiddie to get good results, despite the fact that they did not understand how these scripts work. Compared to Besside-ng, the original Wifite thoroughly used all the tools available to it to attack the network, but at the same time it was very slow.
One of the best features of the original Wifite was that he conducted a WiFi scanning of the area before attacking nearby networks. This allowed the hacker to specify one, several or all networks as targets. Due to the fact that Wifite laid out to the user all the available targets in an easy-to-understand format, even a beginner could understand which attacks are best used against the nearest networks.
The original Wifite could automatically attack WPA networks by intercepting handshakes or use the Reaver tool to bruteforce the WPS PIN codes of nearby networks. Despite the fact that this method of attack was very effective, its execution took 8 hours or more.
The updated WiFite2 works much faster due to the reduction of time for the attacks themselves and the use of more advanced tactics than in the previous version. Because of this, Wifite2 is a more serious and powerful tool for hacking WiFi than the original Wifite.
WiFi hacking procedure
For the fastest possible hacking of nearby networks, Wifite2 uses a simple but fairly effective procedure. He brings every tactic he is trying to apply, to the limit of its practical application, he may even go so far as to try to hack any incoming handshakes.
First of all, Wifite2 scans all channels in search of all networks in the coverage area. Then it ranks the found networks by signal level, since the fact of finding a network does not guarantee a reliable connection with it.
In addition to sorting the detected networks in descending order of signal, the reconnaissance phase includes the collection of information about which hacking methods these networks may be vulnerable to.
Thanks to the organization of Wifite2, you can easily add a directional WiFi antenna, and use Wifite2 to locate the source of any nearby WiFi network when conducting a neighborhood scan.
After the scan is complete, the counties will reflect all reflected targets to see whether clients are connected to them, whether the network announces WPS usage, and what type of encryption the network uses. Based on this, the hacker chooses any target, group or all targets for attack based on the information collected.
Wifite2 will go through the entire list of goals, starting with the fastest and simplest attacks, such as WPS-Pixie, which can crack a password in a matter of seconds, to less reliable tactics, such as checks for using weak passwords using a dictionary attack. If the attack fails or its completion takes too much time, then Wifite2 will proceed to the next possible attack in a particular case, so as not to waste time, as its predecessor did.
What you need
First you need a WiFi adapter that can be switched to monitoring mode. This means that you must choose an adapter that is compatible with Kali Linux. We have several excellent guides on this subject. “ How to determine which WiFi adapter is suitable for Kali Linux ”
and if you need a good wireless card for hacking check this huge list of adapters that support monitor mode, Monitor Mode WiFi adapter
Hackers House Nepal
Disclaimer : In this tutorial, I will automate the wireless cracking process using Wifite step-by-step. This tutorial is only for education purpose, all the demonstrations performed in our own lab. Use at your own risk!!
Wifite is a tool to audit WEP or WPA encrypted wireless networks. It uses aircrack-ng, pyrit, reaver, tshark tools to perform the audit. This tool is customizable to be automated with only a few arguments and can be trusted to run without supervision.
#sudo wifite –dict Desktop/pass.txt –kill // I used my own wordlist "pass.txt", create your own and replace it with your own wordlist.
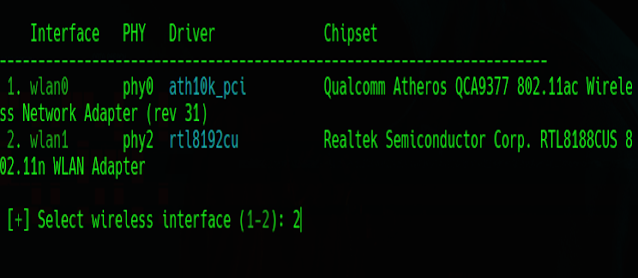
If you have an external wifi card/adapter then it will ask you to choose one to put into monitor mode, choose your wireless interface, and type the number. In my case, "wlan1" is my wifi interface to be operating in monitor mode. So I choose number 2. [Hit Enter]
In this step, you can see all the wifi networks available in my range. After you find the target you wanna hack Press Ctrl+c to stop scanning the wifi networks.

Now you can see all the available networks. Choose the target you wanna hack. In my case, I choose number 1 as my target which is an access point I have configured for testing purposes.[Hit Enter]
Popular Posts

How to report Cyber Crime in Nepal ? – Report it to Cyber Bureau , Bhotahiti Kathmandu – Email as mentioned in site : [email protected] – Website Link : https://www.nepalpolice.gov.np/index.php/cyber-bureau?start=3 – Contact number as seen on site : 9851286770, Phone Number: 014219044 Where can I report cyber crime in Nepal, Online ? – Your all query is already answered above. – If you are still in confusion, then get help via calling 100 . – Or, visit nearest police station and place your query. News Updates : Cyber Crime in Nepal & Report
Tutorial Install WiFite On Kali Linux
WiFite Features
1- WiFite is able to crack the closest access points due to their signal strength first while it sorts targets in dB.
2- De-authenticates clients of hidden networks automatically to reveal SSIDs.
3- It has so many filters to specify what to attack exactly.
4- Timeouts, packets/sec, and other settings are customizable.
5- WiFite can change MAC to a random address before the attack as an anonymous feature. When attacks are complete, change back.
6- It provides the backup of all captured WPA to wifite.py’s current directory.
7- It cycles between all clients and broadcast deauths as a smart WPA de-authentication.
8- You can easily stop the attacks with Ctrl+C and move onto the next target with options to continue or even skip to cracking and exit.
9- You can view the summary of the session at the exit and see the cracked keys.
10- You will find all saved passwords to cracked.txt
11- The built-in updater is available on ./wifite.py-upgrade
Required Tools
1- A wireless card with the ”Monitoring Mode” ability and packet injection.
2- The latest versions of some programs are supported which should be installed to let WiFite work well such as python, iwconfig, ifconfig, Aircrack-ng, airmon-ng, aircrack-ng, aireplay-ng, airodump-ng, packetforge-ng.
3- The suite of programs it uses, forces WiFite to be run as root. While it is not a good idea to run downloaded scripts as root, you can use the Kali Linux bootable Live SC, a bootable USB stick, or a virtual machine. In case you use a virtual machine you need to prepare a wireless USB dongle since they cannot access hardware directly.
Learn Install And Run WiFite On Kali Linux Step By Step
WiFite is designed for the latest version of Kali Linux. If you are using the latest version of the required tools, WiFite can support other pen-testing distributions like BackBox or Ubuntu Server. Now that you got familiar with WiFite enough, it is time to see how easy is to install it on Kali Linux.
Also, you can install WiFite onto your computer (from any terminal) by running:
In this way, you have installed wifite to /user/bin/wifite which is in your terminal path.
Хэндшейк
Это самый актуальный метод, который позволяет получить пароль без постоянного дергания сети. Т.е. you receive a packet, and already the flow offline trying to pick up the password to it using all your computing power – as a result there is no network delay to check the password, no bans from the router, you can really connect all your power – and the output speed of getting the password is increased.
Comrade! I know that you still believe in one-click hacking of any network, but I hasten to disappoint you – it's not true. And even Kali Linux has no power here. There are networks with complex passwords that will take many… years to decrypt.
An experienced hacker should check all actual tools on his own skin, if possible, in order not to get into trouble in a combat environment if one of them fails. Therefore, at any rate will have to know a little bit of theory.
Theory of a Handshake Hack
Here I want to show you the basic steps which are done when using this method. Here is what the pros do:
- Make sure that there is a Wi-Fi adapter. If it is absent, they put an external one.
- Put the adapter in monitoring mode. The adapter must support this. In normal mode, it does not know how to scan the surrounding networks, so you have to do a little work.
- They scan the environment – choose the right network for the attack.
- Begin to "listen" to it. They wait for any user to connect to the network, at which point they intercept the "handshake" packet, which contains an encrypted password. If there are connected users, the process can be accelerated by forcibly kicking the users off the network and catching their connection.
- Purge the intercepted packet for programs that will already be brute-forcing passwords.
- They then shove the cleaned handshake into the brute force attack and try to guess their passwords by brute force or using the prepared dictionary. This stage is usually the longest and can take years, so that the password during this time and can change) But it's still much faster than a simple brute force network. In addition, there are services that already have matching passwords to handshakes – all you have to do is download it, pay for it and get the password.
Phishing
This is another method of gaining access, based on social engineering. The network client is presented with a fake website, for example, asking to update the router software and being asked to enter the Wi-Fi password. In Kali Linux, the most popular tool for this purpose is probably WiFiPhisher.
It is not worth dwelling on the theory here, the attack is specific and designed for the illiteracy of the person on the other end (although for such attacks it is possible to confuse even a competent specialist). So, please watch the video:
Hacking WEP network
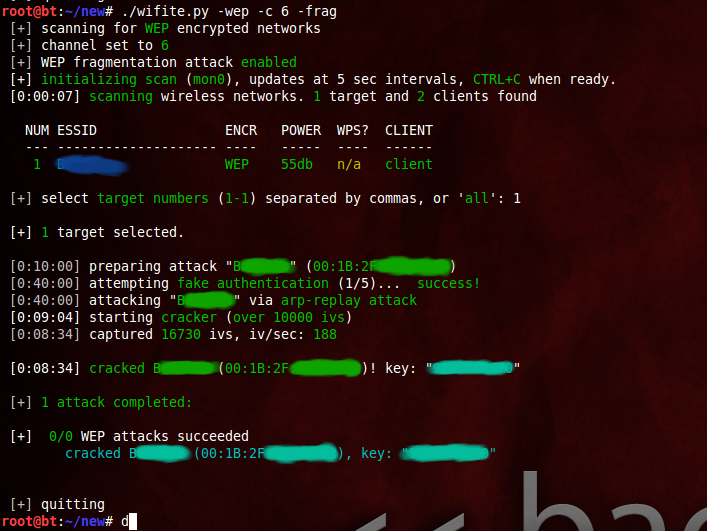
If you've followed my previous posts on Hacking Wifi (WEP), you know there's a lot of homework you have to do before you even start hacking. But not here. With Wifite, its as easy and simple as a single command.
If you see any error at this stage move to the bottom of the page for troubleshooting tips. If your issue is not listed please comment. We reply within a day.
The -wep makes it clear to wifite that you want to hack WEP wifis only. It'll scan the networks for you, and when you think it has scanned enough, you can tell it to stop by typing ctrl+c. It'll then ask you which wifi to hack. In my case, I didn't specify -wep so it shows all the wifis in range.
You can also select all and then go take a nap (or maybe go to sleep). When you wake up, you might be hacking all the wifi passwords in front of you. I typed one and it had gathered 7000 IVs (data packets) within 5 mins. Basically you can except it to hack the wifi in 10 mins approx. Notice how it automatically did the fake auth and ARP replay.
Here are a few more screenshots of the working of Wifite, from their official website (./wifite.py is not something that should bother you. You can stick with the simple wifite. Also, specifying the channel is optional so even the -c 6 was unnecessary. Notice that instead of ARP replay, the fragmentation attack was used, using -frag) –
Hacking WPS wasn't fast (it took hours), but it was easy and didn't require you to do anything but wait.
Troubleshooting
Wifite quits unexpectedly, sating "Scanning for wireless devices. No wireless interfaces were found. You need to plug in a wifi device or install drivers. Quitting."
You are using Kali inside a virtual machine most probably. Virtual machine does not support internal wireless card. Either buy an external wireless card, or do a live boot / side boot with Windows. Anything other than Virtual machine in general.
Read More: