The range advantage of a single base station allows large areas to be covered with fewer stations, which in turn reduces the infrastructure and maintenance costs of LPWAN networks.

- LPWAN and other wireless technologies
- LPWAN-radio channel capacity
- Wi-Fi Networks
- Fifth Generation Cellular Networks (5G)
- AM
- Digital Signal
- An overview of wireless technologies
- Security Recommendations
- Technologies for building industrial wireless networks
- Concurrent Dual-Radio
- Centralized management/easy wireless deployment
LPWAN and other wireless technologies
In IoT and M2M concepts, remote interaction between devices is based on the exchange of small packets of data, and existing wireless technologies are not always able to effectively provide such exchange. LPWAN technology has been specifically designed to provide a simple, reliable, and low-cost means of communication for sensors spread over a large area, covering the needs of speed-independent applications.
LPWAN (Low-power Wide-area Network) is a new type of wireless networks designed to transmit telemetry data of various devices, sensors, sensors and metering devices over long distances. The emergence of LPWAN networks is mainly related to the needs of machine-to-machine (M2M) communication and data transfer within the concept of the Internet of Things (IoT).
The use of wireless technology in a particular area is determined by two key parameters: communication range and data transfer rate (Fig. 1). For example, Wi-Fi, having a high bandwidth of several Mbit / s and a range limit of 100-200 meters, most often used to build wireless LANs within the office, apartment or house.
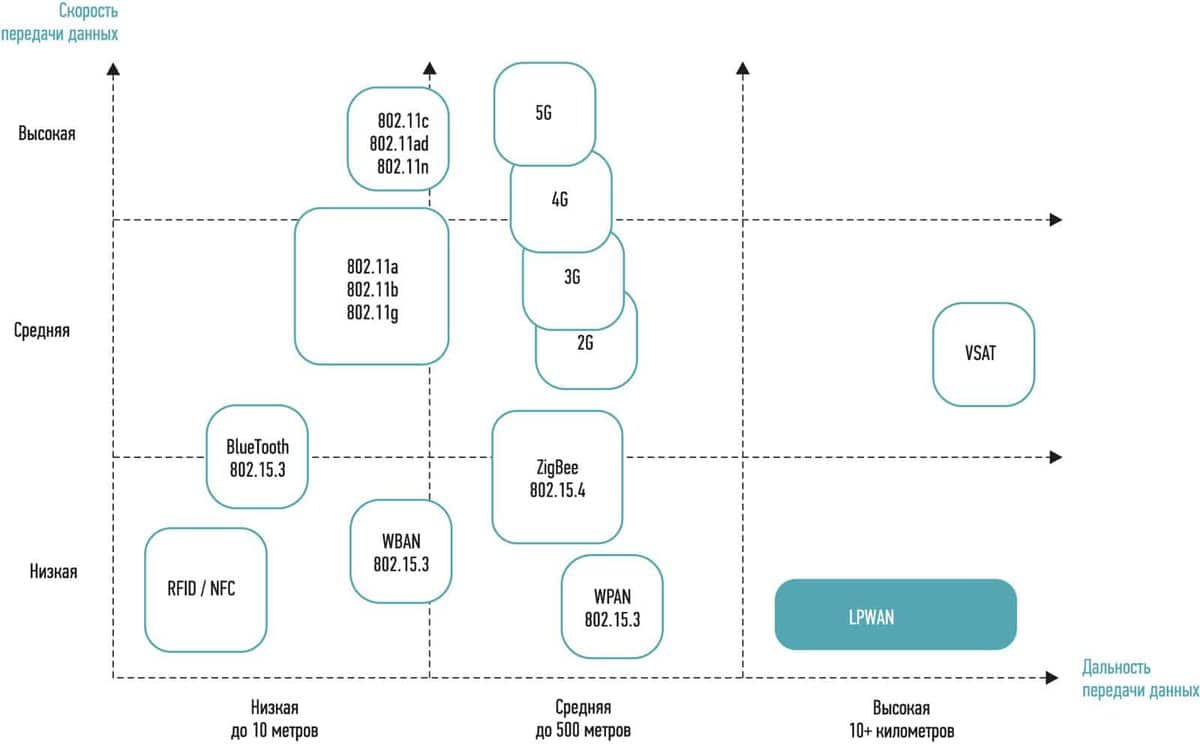
Fig. 1. Comparison of wireless technologies in terms of range and data transfer rate
As follows from the name of the technology, its main characteristics are low power consumption (low-power) and wide-area coverage (wide-area). At the same time features of data transmission in M2M and IoT impose a number of additional requirements for telemetry networks class LPWAN.
- radio transmission range;
- Power efficiency, autonomy;
- data transmission speed;
- radio signal penetration;
- signal transmission delay;
- the number of base stations required to cover a particular area;
- base station performance;
- subscriber fee, connection costs;
- component costs.
LPWAN-radio channel capacity
Inter-machine communication is based on the principle of exchange of small-sized data packets. For example, a smoke detector needs to transmit an alarm when smoke is detected and the result of daily self-diagnostics to the dispatcher – one bit of information. The same is true for sensors in water leakage control systems. Readings of water, electricity, heat, gas meters as well as humidity or temperature sensors can be "packed" into several bits.
The data rate of the LPWAN-radio channel depends on the specific task to be performed and usually ranges from a few bits to several hundred bits per second. There is no need for a high bandwidth link. This, in turn, opens up a number of opportunities to improve other, equally important network parameters.
Wi-Fi Networks
Wi-Fi networks are today, and will remain until at least 2024, the basis of high-performance networks for home and office. In addition to its traditional role, the technology will find application in new developments. For example, as the basis for radar systems or as an element of next-generation two-factor authentication systems.
At the end of 2018, the cross-industry group Wi-Fi Alliance announced the launch of a new version of the standard – IEEE 802.11ax, which was marketed as Wi-Fi 6. The new standard is compatible with previous versions and supports 2.4 GHz and 5 GHz bands. Wi-Fi 6 devices will support Orthogonal Frequency Division Multiple Access (OFDMA). This means it is possible to transfer data simultaneously to multiple clients at an average speed. In addition, the combined operation of MU-MIMO and OFDMA technologies will provide support for up to eight connections at up to 11 Gb/s. In Wi-Fi 5 the number of such connections did not exceed four.
The new Target Wake Time feature of Wi-Fi 6 will provide the ability to set a sleep schedule to conserve battery power.
The introduction of Wi-Fi 6 will significantly increase the density of wireless networks, improving the quality of data exchange in public places with a large number of users per unit area – in transport, corporate offices, trading halls, hotels and stadiums. The first commercial launches of Wi-Fi 6 are scheduled for late 2019.
Fifth Generation Cellular Networks (5G)
The launch of the first fifth-generation (5G) cellular networks began back in 2018, but the first commercial projects at the scale of urban agglomerations or entire countries started only in 2019. In particular, South Korea in April 2019 was the first in the world to launch three commercial 5G mobile networks nationwide at once. In China, commercial operation of 5G networks began in late May.
According to Gartner analysts, it will take five to eight years to deploy 5G networks globally. According to the GSMA forecast, the 5G network in Russia will cover up to 80% of the population already in 2025.
In some cases, fifth-generation cellular networks will complement Wi-Fi networks as a cheaper alternative for high-speed data transmission with dense user populations – such as major cities, airports and manufacturing plants. At first, while 5G technology is still in its infancy, most operators will focus on providing high-speed Internet access services. Nevertheless, the 5G standard has great potential for development, and its subsequent iterations will become the basis for the development of the Internet of Things and a number of other applications, where minimal signal delay during data exchange is critical.
AM
Let's start with a very simple example, the radio signal. The very first type of radio coding that mankind invented was amplitude modulation. Remember the letters AM on old radios. This is it – Amplitude modulation
The coding principle here is elementary. According to the amplitude of the signal, the amplitude of the oscillation changes. It's like if you put a loudspeaker in a pond and you get a big wave from the loud parts. Such a signal is very easy to transmit and decipher.
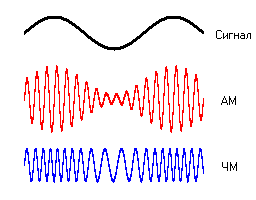
However, it has a disadvantage – it is very sensitive to interference. That is why amplitude modulation did not take root in broadcasting, and it was quickly replaced by frequency modulation, better known to us as FM – Frequency modulation. Here the principle is similar, but instead of the amplitude changes the frequency of oscillation.
Digital Signal
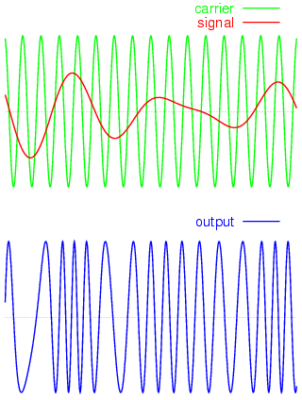
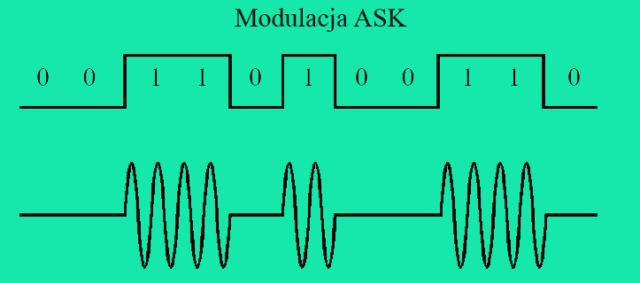
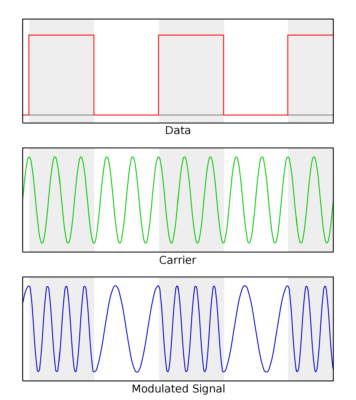
These are examples of analog signals, but a digital signal can also be transmitted by using amplitude or frequency modulation.
It's even simpler and more reliable, because instead of a continuous analog signal, you just have to transmit zeros and ones. There is oscillation – no oscillation for amplitude modulation, high frequency – low frequency for frequency modulation.
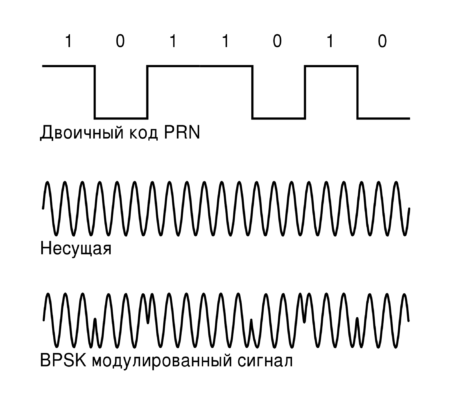
Gaussian Minimum Shift Keying (GMSK))
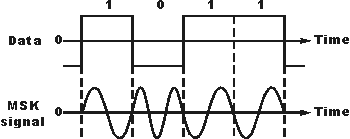
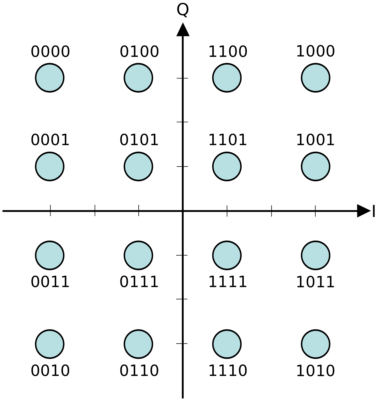
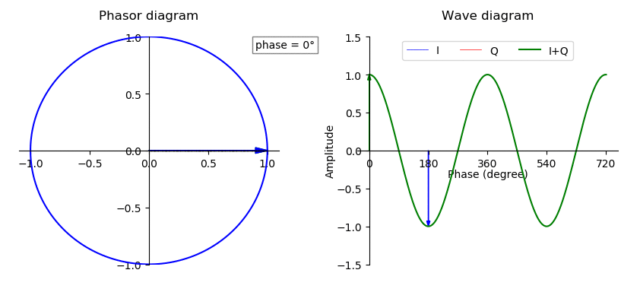
Naturally now coding methods are much more ingenious, in mobile communications and Wi-Fi methods are used orthogonal frequency division (OFDM), as well as quadrature amplitude modulation (QAM).
It all looks much more complicated, but I think you understood the basic principle: with amplitude, frequency, phase of the carrier signal, we can encode a lot of information.
Quadrature Amplitude Modulation, QAM
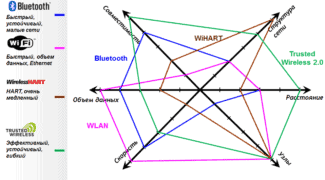
An overview of wireless technologies
Each of the wireless technologies presented on the market has its own characteristics. The choice of one or another solution depends on the tasks the enterprise faces.
Wi-Fi is one of the available and universal technologies. It can quickly transfer large amounts of data, but at the same time the range of coverage is very limited. As a rule, Wi-Fi is not suitable when it is necessary to ensure communication from a mobile moving object, when it is necessary to work with complex applications and when delays in data transfer would be critical for the customer.
If it is fundamentally important for a company to minimize data packet loss, it is better to use MESH technology, which provides a delay of no more than 5 msec. MESH infrastructure is more complex and expensive than Wi-Fi, but MESH-based networks have a higher range (1-2 km, while Wi-Fi has only 300-500 m). MESH supports high data transfer speeds – up to 200 Mbit/s, which is much higher than that of private LTE (pLTE).
Many companies choose pLTE, but we must remember that deploying such networks requires dedicated frequencies and requires an expensive infrastructure (both in terms of the cost of equipment and the cost of owning the network). In any case, pLTE is not suitable when the volume of transmitted data increases significantly on the infrastructure.
The LoRaWan technology stands out. It is responsible for collecting data from a wide range of sensors. For example, this is needed to regularly check the level of humidity, lighting, door status (opening/closing), etc. LoRaWan also collects statistical data about the equipment in the form of a sequence of all possible indicators (engine hours, the amount of fuel in the tank of a diesel generator, etc.). One base station here can cost dozens of times less than in the case of pLTE. But the bandwidth of LoRaWan is quite small – only 10-50 kbit / s, that is, this technology is designed to transmit small amounts of data.
Security Recommendations
Securing wireless networks is a difficult enough task. It is made difficult by the inability to physically isolate intruders from the network or trace their location. However, simple guidelines can go a long way toward insuring your network and minimizing the risk of an attack.
Basic recommendations for securing wireless networks:
- Ensure that the network device is physically protected. The router must be installed so that no interference, such as from a microwave oven, can occur. Also ensure that the reset button cannot be accidentally pressed.
- Change the default login and password. Data for access to the router's configuration interface and Wi-Fi network, are specified in the instructions for the device. It is recommended to change these data by creating a strong password.
- Deny broadcasting the network ID. In that case only the user who knows the network ID will be able to connect to your wireless network.
- Apply filtering by MAC address. Filtering can help limit the number of devices that can connect. It will only allow certain devices with the MAC settings to connect to the network. This measure will make it much more difficult for intruders to access the network and will help eliminate the possibility of "dummy" connections.
- Use effective wireless security protocols. For example, when configuring the router, it is recommended to set the security protocols to WPA/ WPA2.
- Use a firewall on your computer. A software firewall is installed by default on Windows systems starting with XP. Third-party firewalls can be used. A firewall provides control and filtering of traffic to protect against network threats. Therefore, such a company should always be active.
- Use an effective antivirus that is regularly updated.
- Limit the range of the network. Ideally, it is best to limit Wi-Fi coverage only to the confines of your apartment or office. This will make it impossible or very difficult for an intruder to physically access the wireless network.
- Deny access to the router settings via Wi-Fi. In this mode, changing settings requires a cable connection, which means physical access to the network device that is not available to outsiders.
- Avoid using unsecured wireless networks in public places. It is also not advisable to connect to someone else's unprotected network within your home. This could be a false access point used by hackers to steal data.
- Always disconnect your router when you are not using the Internet. This measure will reduce the likelihood of being attacked.
- Use Bluetooth carefully. The feature should be turned off on your phone at all times. It is recommended that you only turn Bluetooth on immediately before using it. Reject connection requests from unknown devices and do not accept any files from them.
Technologies for building industrial wireless networks
To improve the reliability and efficiency of industrial wireless networks, manufacturers widely use their proprietary technologies, which serve to organize the redundancy of wired and wireless channels, high-speed switching (roaming) between neighboring base stations.
Let's take a closer look at these technologies by the example of equipment produced by the Taiwanese company Moxa, one of the leaders in industrial wireless solutions on the Russian market (Fig. 1).

Fig. 1. Conditions of Use of Industrial Access Points and Clients by Moxa Company
Concurrent Dual-Radio
This technology (Fig. 2) is used for data transmission in wireless network without packet loss between base stations and clients. Two independent RF-transceivers simultaneously perform reception / transmission of data packets in the bands 2.4 and 5 GHz, which allows for a noisy air or loss of communication of one of the transceivers to achieve a guaranteed and uninterrupted communication with the receiving party.

Fig. 2. Example of Active concurrent dual-radio technology working.
Let's consider an example of Concurrent Dual-radio technology application at railway station (Fig. 3), where control system of trains traffic is realized with redundant wireless network. Devices placed on the rails allow to determine in real time the position of the train at the station and transmit this information to the central dispatcher's office. A 10-segment fault-tolerant network was deployed for effective control and monitoring of train speed and position. Each segment of the wireless network contains its own local video surveillance system, as well as two AWK-6222 dual RF wireless devices. One device works as an access point, the other as a client. Pairs of AWK-6222 devices create a redundant fault-tolerant client-access point connection. Another AWK-4121 access point in each segment is used to access the IP camera system from mobile devices. Two AWK-6222, one AWK-4121, and an IP camera are connected via a low-power EDS-P308 unmanaged PoE switch powered by solar panels. All AWK units are made to operate in the industrial temperature range and are IP68 rated.
Centralized management/easy wireless deployment
Using centralized management software, system capacity can be increased incrementally as the number of users grows. Also with the help of centralized software performed the procedure of frequency planning and modeling of the wireless network, which allows both a more rational use of private resources, and to establish the minimum required number of access points.
The use of PoE technology in industrial wireless networks supporting the 802.3af PoE standard allows you to place access points in hard-to-reach places, such as on ceilings, walls, where power outlets are not available.
Once again, let us remind you of the main advantages of wireless networks as compared to wired ones:
- significant reduction in the cost of installing sensors;
- No need for preventive maintenance of cables;
- reducing labor costs and time for installation of the system;
- more convenient upgrade of the system.