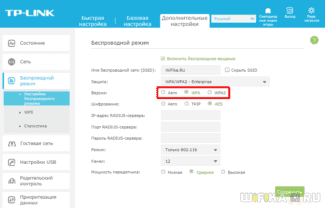
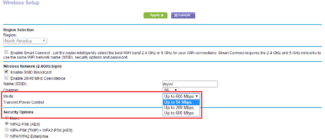
On most routers we've seen, options typically include WEP, WPA (TKIP), and WPA2 (AES) – with WPA (TKIP) + WPA2 (AES) compatibility options. If your router offers WPA2 in either TKIP or AES options, choose AES. Almost all of your devices will work with it, and it's faster and more secure.

- WEP and WPA vs. WPA2: Why the differences for protection matter
- What WEP, WPA, and WPA2 mean – what to use
- Comparison
- Conclusions TheDifference.ru
- WPA vs WPA2: What's the difference between them
- Why would someone choose WPA?
- Why is it important to know about these protocols?
- WEP vs WPA vs WPA2 Personal vs WPA2 Enterprise
- What is WPA3?
- What security protocol does my Wi-Fi network use?
- How to determine the security type of your Wi-Fi network
- Summary of information
- AES vs TKIP
- Wi-Fi Security Modes
- AES vs. TKIP
- Security options for a Wi-Fi network
- Pass me the sugar
- The plan of attack
- WPA2 attacks
- WPA3 attacks
WEP and WPA vs. WPA2: Why the differences for protection matter
The acronyms WEP, WPA, and WPA2 refer to different wireless encryption protocols that are designed to protect the information you send and receive over your wireless network. Choosing a protocol for your own network can be a little confusing if you are not familiar with their differences.
Below is an overview of the history of wireless encryption and a comparison of these protocols so that you can come to a clear conclusion about what you can use for your home or business.
In short, WPA2 is something you should use if possible. Not all devices support it, but if it is available to you, it is important to activate it so that the best possible protection is available to all devices that are currently connected and will connect to your Wi-Fi network.
What WEP, WPA, and WPA2 mean – what to use
These wireless encryption protocols were created by the Wi-Fi Alliance, an association of hundreds of companies in the wireless technology industry. The first protocol created by the group was WEP (Wired Equivalent Privacy), introduced in the late 1990s.
WEP, however, had serious security flaws and was replaced by WPA (Wi-Fi Protected Access). Despite the ease of hacking, WEP connections are still widely used and can give a false sense of security to many people who "secure" their networks with WEP.
The reason WEP is still in use is either because the network administrator has not changed the security settings on the wireless routers, or because the device is outdated and therefore does not support newer encryption methods such as WPA.
Just as WPA replaced WEP, WPA2 has replaced WPA as a more modern and robust security protocol. WPA2 implements the latest security standards, including state-level data encryption. Since 2006, all certified Wi-Fi products must use WPA2 security.
If you're looking for a new wireless card or device, make sure it's labeled Wi-Fi CERTIFIED™ to know it meets the latest security standard. For existing connections, make sure your wireless network uses WPA2, especially when transmitting sensitive personal or business information.
Comparison
Finding the difference between WPA and WPA2 is of no relevance for most users, as the entire wireless network protection comes down to choosing a more or less complex access password. Nowadays the situation is such that all Wi-Fi devices are obliged to support WPA2, so the choice of WPA can be conditioned only by non-standard situations. For example, operating systems older than Windows XP SP3 do not support WPA2 without patches, so machines and devices operated by such systems require the attention of the network administrator. Even some modern smartphones may not support the new encryption protocol, mostly non-branded Asian gadgets. On the other hand, some Windows versions older than XP do not support WPA2 at the level of group policy objects, so they require finer tuning of network connections in this case.

The technical difference between WPA and WPA2 is in the encryption technology, particularly in the protocols used. WPA uses the TKIP protocol, while WPA2 uses the AES protocol. In practice, this means that the more advanced WPA2 provides a higher degree of network security. For example, the TKIP protocol allows you to create authentication keys of up to 128 bits, AES – up to 256 bits.
Conclusions TheDifference.ru
- WPA2 is an improvement of WPA.
- WPA2 uses the AES protocol, WPA uses the TKIP protocol.
- WPA2 is supported by all modern wireless devices.
- WPA2 may not be supported by older operating systems.
- WPA2 is more secure than WPA.
/rating_on.png)
/rating_on.png)
/rating_on.png)
/rating_on.png)
/rating_half.png) (11 ratings, average: 4,36 out of 5)
(11 ratings, average: 4,36 out of 5)
WPA vs WPA2: What's the difference between them
The WPA and WPA2 protocols are the most common security measures used to protect the wireless Internet. With this in mind, we have compared the differences between WPA and WPA2 so that you can find the right option for your situation.
| WPA | WPA2 | |
| Year of manufacture | 2003 | 2004 |
| Encryption method | Temporal Key Integrity Protocol (TKIP) | Advanced Encryption Standard (AES) |
| Security level | Higher than WEP, offering a basic level of security | Higher than WPA, offers an advanced level of security |
| Device support | May support older software | Only compatible with newer software |
| Password length | Shorter password allowed | Longer password required |
| Enterprise use | No company version | Company version available |
| Required computing power | Minimum | More power required |
When comparing WPA and WPA2, the WPA2 protocol is a better option if your device can support it.
Why would someone choose WPA?
The WPA protocol has a less secure encryption method and requires a shorter password, making it a weaker option in terms of security. There is no enterprise solution for WPA because it is not secure enough to support corporate use. However, if you have older software, WPA can be used with minimal processing power and this protocol may be a more viable option for you than the older WEP protocol.
Why is it important to know about these protocols?
All of these wireless standards are designed to keep your home network secure. Each of these protocols has advantages and disadvantages. It is up to the user to choose the right protocol. This article knows exactly which protocol to use at this time.
Keep in mind that wireless technology is inherently insecure because we cannot control the spread of wireless signals in the air. This is why it is important to choose the best security protocol that minimizes the risk of hacking or data leakage.
WEP, WPA and WPA2 Protocol Comparison (Technical Differences)
Protecting your WiFi hotspot is very important, as if it remains insecure, someone could steal your network bandwidth, could hack into your system, or could do illegal activity through your network. WiFi protocols are standards that were created to provide safe and secure access to WiFi wireless communications. WiFi protocols encrypt data when it is transmitted over the network. A person without a decryption key cannot connect to the network and read communication information.
Some well-known WiFi protocols include WEP, WPA, WPA2 (Personal and Enterprise). In this article, we will discuss the technical differences between these protocols and when each will be used.
WEP vs WPA vs WPA2 Personal vs WPA2 Enterprise
Instead of discussing each security protocol, we will discuss three factors and compare the protocols according to those factors. The factors include security, authentication, and performance.
WEP and WPA use the RC4 algorithm to encrypt network data. RC4 is inherently insecure, especially in the case of WEP, which uses small keys and key management. Because WEP sends passwords in text form over the network, it is fairly easy to hack the network using network sniffers.
WPA was developed as a temporary alternative to WEP. A secure form of WPA uses TKIP encryption, which encrypts passwords for network communication. Although it is also a weaker form of security, it is much better than WEP.
WPA2 was designed for network communication with complete security. It uses AES-CCMP encryption, which could theoretically take hundreds of years to break. All communication packets sent and received through WPA2 are encrypted.
Although WPA2 is the best form of security, you can use WPA where devices are not compatible with WPA2 and use WEP as a last resort because it is still better than a completely open network.
Authentication is an important part of wireless network communication. It determines whether or not the user is allowed to communicate with the network. All three security protocols, WEP, WPA and WPA2 use PSK (pre-shared key) for authentication. Although WEP uses a simple PSK, WPA and WPA2 combine it with other encryption methods, such as WPA-PSK and EAP-PSK, to make the authentication process more secure. The WPA and WPA2 standard for authentication is 802.1x / EAP.
WPA and WPA2 use 256-bit encryption for authentication, which is quite secure. But because users tend to have trouble setting such long passwords, the passphrase can range from 8 to 65 characters, which is combined with EAP for encryption and authentication.
What is WPA3?
WPA3 is the third version of the Wi-Fi protected access protocol. The Wi-Fi Alliance released WPA3 in 2018. The WPA3 protocol includes the following new features for personal and corporate use:
Individual data encryption. When logging onto a public network, WPA3 registers a new device in a way that does not involve the use of a shared password. WPA3 uses DPP (Device Provisioning Protocol) for Wi-Fi networks, allowing users to use NFC tags or QR codes to connect devices to the network. In addition, WPA3 uses GCMP-256 encryption for security instead of the previous 128-bit encryption.
SAE protocol (simultaneous peer authentication). This protocol is used to create a secure "handshake" in which a network device connects to a wireless access point and both devices exchange data to verify authentication and connection. Even if the user's password is not strong enough, WPA3 provides more secure DPP communication for Wi-Fi networks .
Enhanced protection against password brute force attacks. The WPA3 protocol protects against password brute force attacks offline. The user is allowed to make only one password attempt. In addition, you must interact directly with the Wi-Fi device: physical presence is required for each password attempt. WPA2 lacks built-in encryption and data protection in public open networks, making password brute force attacks a serious threat.
WPA3 devices became widely available in 2019. They are backward compatible with WPA2 devices.
What security protocol does my Wi-Fi network use?
To ensure the proper level of security for your Wi-Fi network, it's important to know what type of encryption it uses. Legacy protocols are more vulnerable than newer ones, so they are more likely to be compromised. Legacy protocols were developed before it was fully understood how attackers were targeting routers. Newer protocols address these vulnerabilities, so they are considered to provide better security for Wi-Fi networks.
How to determine the security type of your Wi-Fi network
- Locate the Wi-Fi connection icon in your taskbar and click on it.
- Then tap Properties . under the current Wi-Fi connection.
- Scroll down and locate the Wi-Fi connection information under Properties.
- Underneath it, find Security Type, which displays your Wi-Fi protocol information.
- Hold down the Option ..
- Tap on the Wi-Fi icon icon in the toolbar.
- This displays information about your Wi-Fi network, including its security type.
- On your Android phone, go to settings..
- Open the Wi-Fi ..
- Select the router you're connected to and see information about it.
- The Wi-Fi network security type is displayed.
- The path to this screen may vary from device to device.
Unfortunately, iOS does not allow you to check the security of your Wi-Fi network. To check the security level of your Wi-Fi network, you can use your computer or log in to your router through your phone. All router models are different, so you may have to consult your device's documentation. If your router is set up by your Internet service provider, you can ask them for help.
Summary of information
| WEP (1997) | WPA (2003) | WPA2 (2004) | WPA3 (2018) | |
|---|---|---|---|---|
| Encryption | RC4 | RC4+TKIP | AES+CCMP | AES+GCMP-256 |
| Authentication | SharedKey | PSK | PSK | SAE |
| Data Integrity | CRC-32 | MIC | CBC-MAC | BIP-GMAC-256 |
| Key management | none | 4way handshake | 4way handshake | ECDH and ECDSA |
You can now protect your Wi-Fi network with WPA2but you need to use modern hardware (router and device with updated OS) and take care of a complex password.
But if you bought a router that supports WPA3 and you have a modern smartphone (Android 10 and above, IOS 13 or later) or laptop (Windows 10 or later), you can start using WPA3.

In this article we will walk you through the technologies that are responsible for securing Wi-Fi, namely WEP, WPA, WPA1, WPA2 and WPA3
AES vs TKIP
TKIP and AES – are two different types of encryption that can be used by Wi-Fi networks.
TKIP is an older encryption protocol introduced with WPA to replace the insecure WEP encryption. TKIP is actually very similar to WEP encryption. TKIP is no longer considered secure and is considered obsolete.
AES is a more secure encryption protocol introduced with WPA2. AES is not some rigid standard designed specifically for Wi-Fi networks. It is a serious global encryption standard that is used even by government agencies. For example, when you encrypt a hard drive with TrueCrypt, AES encryption can be used to do so.
AES is considered quite secure, and the main drawbacks can be susceptibility to brute force attack and security breaches in other aspects of WPA2.
The short explanation is that TKIP is an older encryption standard used in the old WPA. AES is the new Wi-Fi encryption solution used by the new and secure WPA2 standard. Theoretically, that's the end of it! But, depending on your router, choosing WPA2 may not be a good enough solution.
While WPA2 should use AES for optimal security, it can also use TKIP when backward compatibility with legacy devices is needed. In this state, devices that support WPA2 will connect to WPA2 and devices that support WPA will connect to WPA. Therefore, "WPA2" does not always mean WPA2-AES. However, on devices without a visible "TKIP" or "AES" option, WPA2 is usually synonymous with WPA2-AES.
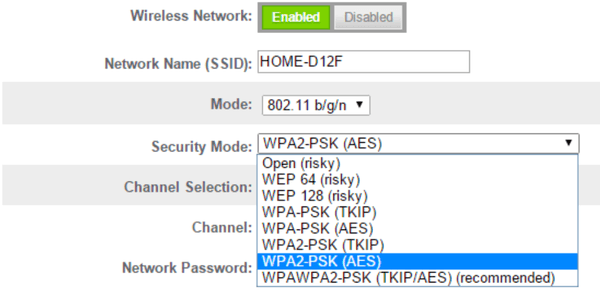
Wi-Fi Security Modes
Not confused yet? All you really have to do is pick one, the most secure option on the list that works with your devices.
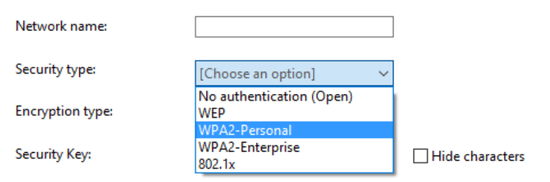
Here are the options you're likely to see on your router:
- Open (risky): There is no passphrase in open Wi-Fi networks. You should not set up an open Wi-Fi network – it is like taking the lock off the front door.
- WEP 64 (risky): The old WEP protocol standard is vulnerable and you should not use it.
- WEP 128 (risky): this is the same WEP but with a larger encryption key size. In fact, it is as vulnerable as WEP 64.
- WPA-PSK (TKIP): The original version of the WPA protocol (essentially WPA1) is used. It has been replaced by WPA2 and is not secure.
- WPA-PSK (AES): the original WPA protocol is used, but TKIP has been replaced by the more modern AES encryption. It is offered as an intermediate option: devices that support AES will almost always support WPA2, and devices requiring WPA will almost never support AES encryption. Thus, this option makes little sense.
- WPA2-PSK (TKIP): uses the modern WPA2 standard with the old TKIP encryption. This is not secure and is suitable if you have older devices that cannot connect to a WPA2-PSK (AES) network.
- WPA2-PSK (AES): This is the most secure option. It uses WPA2, the latest Wi-Fi encryption standard and the latest AES encryption protocol. You must use this option. On some devices, you will just see the option "WPA2" or "WPA2-PSK". If you do, you will probably use AES as it is a common sense choice.
- WPAWPA2-PSK (TKIP/AES): Some devices offer and even recommend this mixed-mode option. This option allows you to use both WPA and WPA2 with both TKIP and AES. This provides maximum compatibility with any ancient devices you may have, but also allows attackers to penetrate your network by compromising the more vulnerable WPA and TKIP protocols.
AES vs. TKIP
TKIP and AES are two different encryption standards that can be used in Wi-Fi networks. TKIP is an older encryption protocol introduced by the WPA standard to replace the highly unreliable WEP algorithm. In fact, TKIP is similar to WEP in many ways. TKIP is no longer considered a secure method of protection and is no longer recommended. In other words, you should not use it.
AES is a stronger encryption protocol introduced by the WPA2 standard. AES is not some dull, this or that standard designed specifically for Wi-Fi networks. It's a serious global encryption standard, adopted even by the U.S. government. For example, when you encrypt your hard drive with TrueCrypt, it can use the AES encryption algorithm to do so. AES is a widely recognized standard, providing almost complete security, and its possible weaknesses are the potential susceptibility to brute force attacks (which are countered by fairly complex passphrases) and the security flaws associated with other aspects of WPA2.
A truncated version of the protection is TKIP, an older encryption protocol used by the WPA standard. AES for Wi-Fi is a newer encryption solution used in the new and secure standard WPA2. In theory, that would be the end of it. But in practice, depending on your router, simply choosing WPA2 might not be enough.
Although the WPA2 standard involves the use of AES for optimal security, it can also use TKIP – where backward compatibility with previous generations of devices is required. In this case, devices that support WPA2 will connect according to WPA2, and devices that support WPA will connect according to WPA. That is, "WPA2" does not always mean WPA2-AES. However, on devices without explicit "TKIP" or "AES" options, WPA2 is usually synonymous with WPA2-AES.
The abbreviation "PSK" in the full name of these options stands for "pre-shared key" – your passphrase (cipher key). This distinguishes personal standards from WPA-Enterprise, which uses a RADIUS server to issue unique keys to large corporate or government Wi-Fi networks.
Security options for a Wi-Fi network
- Open (risky).: There are no passphrases on open Wi-Fi networks. You should not set this option – seriously, you could give the police an excuse to raid your place.
- WEP 64 (risky).: The old standard WEP protocol is easily vulnerable, and you should not use it.
- WEP 128 (risky): This is the same as WEP, but with a longer encryption key length. In fact, it is no less vulnerable than WEP 64.
- WPA-PSK (TKIP): This uses the original version of the WPA protocol (in fact, WPA1). It is not fully secure and has been replaced by WPA2.
- WPA-PSK (AES): the original WPA protocol is used here, with TKIP replaced by the more modern AES encryption standard. This option is offered as a temporary measure, but devices that support AES will almost always support WPA2, while devices that require WPA will almost never support AES. Thus, this option does not make much sense.
- WPA2-PSK (TKIP): This uses the current WPA2 standard with the old TKIP encryption algorithm. This option is not secure and its only advantage is that it is suitable for old devices which do not support the WPA2-PSK (AES) option.
- WPA2-PSK (AES): This is the most common security option. It uses WPA2, the latest encryption standard for Wi-Fi networks, and the latest AES encryption protocol. You should use this option. On some devices, you will see an option called simply "WPA2" or "WPA2-PSK", which in most cases implies the use of AES.
- WPAWPA2-PSK (TKIP/AES): Some devices offer – and even recommend – this mixed option. This option allows you to use both WPA and WPA2 with both TKIP and AES. This provides maximum compatibility with any ancient devices you may have, but also gives hackers the ability to penetrate your network by hacking into the more vulnerable WPA and TKIP protocols.
WPA2 certification has been valid since 2004, becoming mandatory in 2006. Any device bearing the "Wi-Fi" logo manufactured after 2006 must support the WPA2 encryption standard.Pass me the sugar
Imagine that you are a device that receives instructions. Anyone can connect to you and give you any command. Everything is fine, but at some point you have to filter out the personalities who can control you. This is where the fun part comes in.
How do you figure out who can give a command and who can't? The first thing that comes to mind is by password. Have each client give some kind of password before giving a new command. That way, you will only execute commands which were followed by the correct password.
The rest are screwed.
That's how the HTTP basic authorization (Auth Basic) works:
AuthType Basic AuthName "My super secret zone!" AuthUserFile /home/.htpasswd Require valid-user
After successful authorization, the browser will just pass a certain header on every request to the closed zone:
This approach has one big disadvantage – since the password (or login-password, which is essentially just two parts of the same password) is transmitted over the channel "as is" – anyone can get in between you and the client and get your password on a platter. And then use it and dispose of you however they want!
To prevent this nuisance, you can resort to a ruse: use some two-way encryption algorithm, with our password as a private key, and never share it explicitly. However, this will not solve the problem – it is enough to know the password once and you can decrypt any data transmitted in the past and in the future, plus encrypt your own and successfully masquerade as a client. Considering that the password is intended for a human and that people are not inclined to use the entire 256-byte set of symbols, and that these symbols are usually about 6-8… well, the Komsomol will not approve.
The plan of attack
Attentive readers, of course, have noticed that no matter how cunning we are, we can't get away from transmitting the password and the temporary key in plain or hashed form. As a result, all a hacker needs to do is intercept the transmission at this phase, and he can read all the subsequent data and participate in the process by inserting his five kopecks. And it is impossible to tell the difference, because all the information that would guide the server for issuing a temporary key or access verification is based exactly on what was at the beginning of the transmission – the handshake. So the hacker knows everything the server and the client know, and can fool both until the temporary key expires.
Our job in hacking any transmission somehow comes down to intercepting the handshake, from which we can either pull the temporary key, the original password, or both. All in all, it's a pretty long undertaking and requires a certain amount of luck.
WPA2 attacks
Since the protocol is an improvement of an already existing protocol, so part of the attacks from WPA for it are still valid. This protocol, unlike previous ones, is still relevant, it is used by the default access points. The cryptography to provide access to the point and the encryption of data on the network is well implemented in the documentation, but the implementation on the devices contains certain costs, which are used by tools to obtain data on the access key and the decryption of traffic. And so the list of attacks:
The result of each attack is a key that allows access to Wi-Fi.
The tools to perform the attacks are all the same ones listed for WPA and additionally Bettercap. This tool will automatically collect all data into a dump and save it to disk for further bruteforcing. The bruteforcing can be done either via the aircrack package or via hashcat.
WPA3 attacks
The most recent version of the security protocol for Wi-F, although it was created in 2018, is still conquering the market of access points and network cards. The protocol takes into account all the shortcomings of the previous ones and is theoretically the most secure. There are no attacks to recover the encryption key and gain full access to the system. There are only variations of denial-of-service attacks in which a switch to previous versions of the security algorithms can be made.
That is, the following set of tools can be used to search for hidden access points and test them from a security point of view:
- bettercap for conducting mitm attacks and key recovery attacks;
- aircrack package for performing key recovery and denial of service attacks;
- eaphammer for key recovery;
- Bully – for WPS bruteforcing.
In today's world, cybersecurity comes first. Increasing cyber attacks on businesses, cyber warfare, and the ease of implementing fraud schemes present us with new challenges every day. How do you build your own security loop? Let's talk about it at a free webinar with Sergey Tereshin, a teacher of the "Network Security" course.