Mass adoption of WPA3 will occur over the next few years, as devices do not need to be certified for WPA3, according to WiFi Alliance rules, in the next two years. During this period, the new protocol will be an optional feature in devices that support WPA2.
- Type of wireless security and encryption. Which one to choose?
- Wi-Fi security: WPA3, WPA2, WEP, WPA
- Simultaneous Authentication of Equals (SAE)
- 192-bit security protocols
- What is WPA?
- What is WPA2?
- WPA2
- WPA3.
- WPA3 and WPA2 protocol compatibility
- Addressing Key Problems
- What is Wi-Fi Easy Connect?
- Wi-Fi security is important
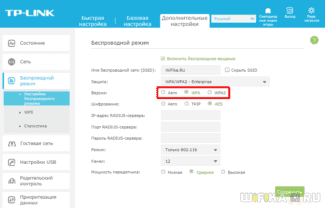
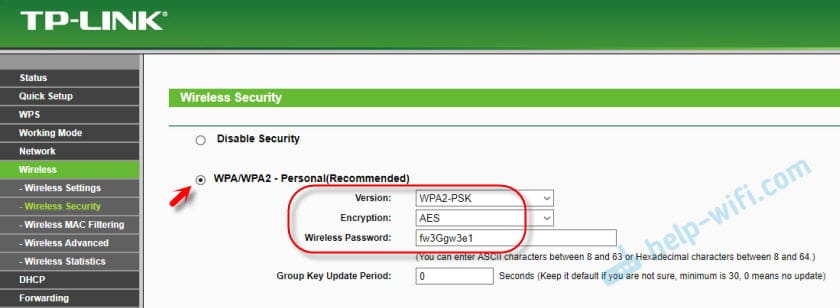
Type of wireless security and encryption. Which one to choose?
To protect your Wi-Fi network and set a password, you must necessarily choose a wireless security type and encryption method. And at this point many people have a question: which one should I choose? WEP, WPA, WPA2, or WPA3? Personal or Enterprise? AES, or TKIP? What security settings will best protect your Wi-Fi network? In this article, I will try to answer all of these questions. Let's take a look at all of the authentication and encryption methods that are available. Let's find out what Wi-Fi security settings are best for your router.
Note that security type, or authentication, network authentication, security, authentication method are all the same thing.
Authentication type and encryption are the basic security settings for a wireless Wi-Fi network. I think we should start by figuring out what they are, what versions there are, their capabilities, etc. After that we will figure out what type of security and encryption to choose. I will show you an example of some popular routers.
I strongly recommend that you set up a password and protect your wireless network. Make it as secure as possible. If you leave your network open and unsecured then anybody can connect to it. This is not very secure in the first place. As well as the unnecessary load on your router, connection speeds drop and all sorts of problems with the connection of various devices.
Wi-Fi security: WPA3, WPA2, WEP, WPA
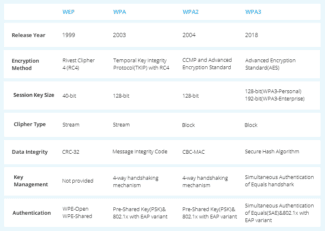
There are three security options. Of course, not counting "Open" (No protection) .
- WEP (Wired Equivalent Privacy) is an outdated and insecure authentication method. It is the first and not very successful method of protection. Attackers have no problem accessing wireless networks that are protected by WEP. You do not need to set this mode in your router's settings, although it is there (not always).
- WPA (Wi-Fi Protected Access) – reliable and advanced type of security. Maximum compatibility with all devices and operating systems.
- WPA2 – Improved and more secure version of WPA. There is support for AES CCMP encryption. This is the current version of the protocol, which is still used on most home routers.
- WPA3 – is a new standard that allows for greater protection against attacks and provide stronger encryption than the previous version. OWE encryption also increases the security of public open networks. It was introduced in 2018 and is already actively used on almost all modern routers and clients. If your devices support this version, use it.
- WPA/WPA2 – Personal (PSK) – is a common method of authentication. When you only need to set a password (key) and then use it to connect to the Wi-Fi network. One password is used for all devices. The password itself is stored on the devices. Where it can be viewed or changed if necessary. It is recommended to use this option.
- WPA/WPA2 – Enterprise – A more sophisticated method used mainly for securing wireless networks in offices and establishments. It provides a higher level of security. It is only used when a RADIUS server (which issues passwords) is installed for device authentication.
Simultaneous Authentication of Equals (SAE)
The biggest change that WPA3 will bring. The most important moment in network security comes when a new device tries to establish a connection. The enemy must stay out of the gate, so WPA2 and WPA3 pay a lot of attention to authenticating new connections and ensuring that they are not attempts by a hacker to gain access.
SAE is a new method of authenticating a device attempting to connect to a network. SAE is a variant of the so-called dragonfly handshake which uses cryptography to prevent an intruder from guessing the password. It tells the new device or the user how to "greet" the network router when exchanging cryptographic keys.
SAE replaces the Pre-Shared Key (PSK) method [pre-shared key] used since WPA2 was introduced in 2004. PSK is also known as four-step linking, because that's how many messages, or two-way "handshakes," need to be sent between the router and the connecting device to confirm that they have agreed on a password, without either party telling the other. PSK seemed secure until 2016, and then a Key Reinstallation Attacks (KRACK) was discovered.
KRACK interrupts a series of handshakes by pretending that the connection to the router has been temporarily severed. It actually uses repeated connection opportunities to analyze the handshakes until it can guess what the password was. SAE blocks the possibility of such an attack, as well as the most common offline dictionary attacks, where a computer goes through millions of passwords to determine which one fits the information obtained during PSK connections.
As the name implies, SAE works on the assumption of device equality, rather than treating one device as sending requests and the other as establishing the right to connect (traditionally it was the device trying to connect and the router, respectively). Either party can send a connection request, and then they start sending authentication information independently, instead of exchanging messages back and forth one by one. And without that exchange, a KRACK attack would have no way to "put a foot between the door and the jamb," and dictionary attacks would become useless.
192-bit security protocols
WPA3-Enterprise, the version of WPA3 designed for government and financial institutions as well as corporate environments, has 192-bit encryption. This level of encryption would be redundant for a home router, but it makes sense for networks dealing with particularly sensitive information.
Right now, Wi-Fi works with 128-bit security. 192-bit security would not be mandatory – it would be a configuration option for those organizations whose networks would need it. The Wi-Fi Alliance also emphasizes that industrial networks need to beef up security on all fronts: the resilience of a system is determined by the resilience of the weakest link.
To ensure the appropriate level of security for the entire network, from start to finish, WPA3-Enterprise will use 256-bit Galois/Counter Mode for encryption, a 384-bit Hashed Message Authentication Mode for key creation and validation, and Elliptic Curve Diffie-Hellman exchange, Elliptic Curve Digital Signature Algorithm for key authentication. There's a lot of complicated math involved, but the upside is that 192-bit encryption will be supported at every step.
What is WPA?
WPA (Wi-Fi Protected Access) is a protocol that appeared in 2003, with which the Wi-Fi Alliance replaced the WEP protocol. WPA is similar to WEP, but includes enhanced security key handling and user authentication. WEP provides all authorized systems with a single key, while WPA uses Temporal Key Integrity Protocol (TKIP), which dynamically changes the key used by systems. This prevents attackers from creating their own encryption key to match the one used on the protected network. The TKIP encryption standard was later replaced by the Advanced Encryption Standard (AES).
The WPA protocol also includes message integrity checking to determine if data packets have been hijacked or altered by an intruder. The WPA protocol uses 256-bit keys, which are significantly more secure than the 64- and 128-bit keys used by the WEP protocol. However, despite these improvements, vulnerabilities were discovered in the WPA protocol, which led to the creation of the WPA2 protocol.
Sometimes the term "WPA key" is used to refer to the password used to connect to a wireless network. The WPA password can be obtained from the network administrator. In some cases, the default WPA password can be printed on the wireless router. If you are unable to determine the router's password, you may be able to reset it.
What is WPA2?
The WPA2 protocol was introduced in 2004. It is an updated version of WPA. WPA2 is based on a high security network (RSN) mechanism and works in two modes:
- Personal or shared key mode (WPA2-PSK) – uses a common access password and is usually used in home networks.
- Enterprise mode (WPA2-EAP) – is more suitable for corporate and commercial networks.
Both modes use the CCMP protocol, which is based on the Advanced Encryption Standard (AES) algorithm for message authentication and integrity. CCMP is more secure than the original TKIP protocol used in WPA, so its use makes it more difficult for attackers to penetrate.
However, the WPA2 protocol also has disadvantages. For example, it is vulnerable to key resetting attacks (KRACK). Key resetting attacks exploit a WPA2 vulnerability that allows simulating a real network and forcing users to connect to a malicious network instead of a real one. This allows attackers to decrypt small pieces of data, which, when combined, allow the encryption key to be compromised. However, patches can be installed on devices, so WPA2 is considered more reliable than WEP and WPA.

WPA2
Soon in the algorithm TKIP was also found to have problems, but already in 2004 the WPA2.
WPA2 used a different type of encryption: AES. This is an encryption standard which is widely used around the world, and not just in Wi-Fi. This algorithm has been well analyzed. For Wi-Fi, it has been augmented with the CCMP algorithm (Counter/CBC-MAC), i.e. TKIP was replaced by CCMP.
In turn, the algorithm CCMP has replaced the consistency check algorithm with MIC to CBC-MAC (Cipher Block Chaining Message Authentication Code). This is an even more advanced algorithm that protected messages from accidental corruption or from intentional tampering.
The developers left the authentication method (PreSharedKey) and the key management algorithm (4way handshake).
Cryptography algorithm AES is considered reliable even nowadays. But in the key management algorithm (4way handshake) found a problem in 2016. It allowed an attack called Key Reinstallation Attacks. This attack allows obtaining the encryption key of traffic and decrypting it (listening). To change the data being transmitted, however, if the AES+CCMP, it is impossible to change the transmitted data. After that, operating systems have released updates to close this vulnerability, although it remained on old routers (which have not been updated).
Thus, it is currently safe to use WPA2 (AES+CCMP). But you need to use a modern Wi-Fi router and a modern client that has had this vulnerability removed.
WPA3.
Relatively recently, in 2018, the WPA3 .. It uses everything state-of-the-art that has been invented in cryptography.
The encryption algorithm AES is kept, but replaced by CCMP with . GCMP-256 (Galois/Counter Mode Protocol) to encrypt transmitted data.
The developers also changed the authentication process and key management. So PreSharedKey has been replaced by the SAE (Simultaneous Authentication of Equals). А SAE, in turn, brought a new key management algorithm, ECDH (Elliptic curve Diffie-Hellman) and ECDSA (Elliptic Curve Digital Signature Algorithm).
All of these (SAE, ECDH, ECDSA) are very complex mathematical algorithms, but they are in addition to the encryption algorithm AES+GCMP-256 make a Wi-Fi network very secure.
To protect the integrity of the data began to use an even more advanced algorithm – BIP-GMAC-256..
To protect the network from password brute force attacks the WPA3 standard has introduced a limit on the number of authentication attempts per handshake. This limitation prevents offline password brute-forcing. Also, even knowing the password, an intruder will not be able to decrypt previously intercepted traffic.
WPA3 and WPA2 protocol compatibility
The WPA3 protocol retains two modes of operation: WPA3-Enterprise for enterprise use and WPA3-Personal for other uses. At the same time, all networks using WPA3 prohibit the use of legacy protocols and simultaneously require the use of secure management frames (PMF). Simply put, WPA3 "clears the field" of less secure solutions, and in the future all new WiFi devices will have at least WPA3 protection.
However, in the coming "transition" years, WPA3 and WPA2 compatibility will remain, as WPA2 is still mandatory for all WiFi devices. Thus, devices with WPA3 will be able to connect to networks with WPA2. But WPA3 protection is only available if the network and devices support WPA3.
In addition to the WPA3 protocol, there are two separate features: Easy Connect for connecting IoT and devices with limited or no display interface, and Enhanced Open for open networks (airports, restaurants, guest areas, etc.). It is important to note that these are separate WPA3 certification programs, and they are not included into the structure of the WPA3 protocol.
The point of this division is that in each scenario the most reliable and least resource-intensive approach to data protection is used. At the same time, the separation reduces confusion. For example, Enhanced Open users are not strictly authenticated with the WPA3 network protocol and are therefore more vulnerable. That's why Open networks are separated, outside of WPA3.
Enhanced Open needs special attention. Future routers and access points with WPA3 will in most cases have the Enhanced Open option and include it when WPA3 is not in use. Most modern devices do not indicate to users the type of WiFi network protection, so errors in security assessment can occur. In the future, hardware and software manufacturers will probably solve this problem with appropriate indications and alerts. It should be noted that despite being less secure, Enhanced Open still prevents users of open networks from intercepting other people's traffic, sessions, and other attacks.
Addressing Key Problems
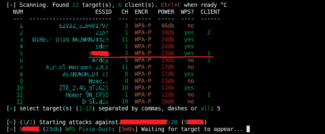
Over the past decade, the WPA2 protocol has been repeatedly hacked, and in general is no longer effective enough to protect sensitive data. Particularly, WPA2 depends on the complexity of a password, which can be cracked by brute-forcing. After obtaining the necessary data from the network, cybercriminals can guess passwords offline and remain undetected. It is especially risky to use WPA2-Personal mode in corporate networks, as intruders can gain access to network traffic monitoring and attack users with access to sensitive information.
WPA2-Enterprise mode is more reliable, but requires properly configured RADIUS server and appropriate additional tools.
WPA2 protocol is most vulnerable for open networks, as it does not have any built-in encryption system, and there is a risk of leakage of passwords from accounts, accounts in Internet services, etc.
The WPA3 protocol addresses these major vulnerabilities of WPA2, making off-line bruteforcing impossible and making the level of security dependent on the complexity of the WiFi password. However, remember that easy-to-guess passwords, such as "admin", "1234", etc., will still be unacceptable.
Capabilities and technologies
WPA3 uses the new Simultaneous Authentication of Equals (SAE) authentication method instead of the old Pre-Shared Key (PSK). The new Simultaneous Authentication of Equals (SAE) method does not use the Pre-Shared Key (PSK). Therefore, it is impossible to hack networks with WPA3 by simply going through the password variants offline, that is, without attracting attention.
In addition, and in WPA3-Personal mode provides individual encryption, which prevents users from tracing other people's traffic, even if they have a password and successfully connect to the WiFi network.
WPA3-Enterprise has additional protection with 192-bit encryption, making this mode suitable for handling sensitive data of commercial and government organizations.
What is Wi-Fi Easy Connect?
Wi-Fi Easy Connect – is a new connectivity standard designed to "simplify the preparation and setup of Wi-Fi devices."
As part of this, Wi-Fi Easy Connect offers strong public-key encryption for every device added to the network, even those with "virtually no user interface, such as smart home and IoT products.
For example, on your home network, you would specify one device as the central configuration point. The central configuration point would be a multimedia device such as a smartphone or tablet.
The multimedia device is then used to scan a QR code, which in turn triggers the Wi-Fi Easy Connect protocol developed by the Wi-Fi Alliance.
Scanning the QR code (or entering a code specific to the IoT device) gives the connected device the same protection and encryption as other devices on the network, even if direct setup is not possible.
Wi-Fi Easy Connect combined with WPA3 will greatly enhance the security of IoT networks and smart home devices.
Wi-Fi security is important
Even as of this writing, WPA2 remains the most secure method of encrypting Wi-Fi, even taking into account the KRACK vulnerability. While KRACK is certainly a problem, especially for corporate networks, home users are unlikely to encounter such an attack (unless, of course, you are a decent person).
WEP is very easy to hack. You should not use it for anything . Moreover, if you have devices that can only use WEP security, you should consider replacing them to improve the security of your network. Learn how to check the Wi-Fi security type to determine the type to make sure you are not using WEP.
It's also important to note that WPA3 won't magically appear and protect all your devices overnight. There is always a long period between the introduction of a new Wi-Fi encryption standard and its widespread adoption.
The level of adoption depends on how quickly manufacturers patch devices and how quickly router manufacturers use WPA3 for new routers.
For now, you should focus on securing your existing network, including WPA2. A great place to start is to check the security of your router. See our guide to finding and changing your Wi-Fi password. for some basics.
Read More: